Course: Certified Ethical Hacker (CEHv12)
duration: 73 hours |
Language: English (US) |
access duration: 180 days |

Details
An Ethical Hacker attempts to systematically inspect network infrastructures, with the owner's permission, to detect security vulnerabilities that a malicious hacker could potentially exploit. They assess the security status of an organization by identifying vulnerabilities in the network and system infrastructure to determine whether unauthorized access is possible.
This course will teach you the latest hacking tools, techniques, and methodologies used by hackers and information security professionals to lawfully hack an organization.
Result
After completing the training you have the right knowledge to
ethically hack. You are also fully prepared for the EC-Council
Certified Ethical Hacker v12 exam.
An exam voucher is not included in this course.
Prerequisites
You have 2 years of work experience as an IT security specialist. You have also a technical background with a good knowledge of networking and networking concepts.
Target audience
Security Specialist
Content
Certified Ethical Hacker (CEHv12)
CEH v12: Cybersecurity Concepts, Attacks, and Information Warfare
Building a strong foundation of knowledge is crucial to becoming an effective cybersecurity professional. In this course, you'll build that foundational knowledge by exploring the five core elements of cybersecurity. You'll examine how classifying what motivates an attacker to attack a network or system can go a long way into figuring out how to best protect systems and networks. Next, you'll explore the many types of attacks that threat actors use to gain access to systems and sensitive data. Finally, you'll learn about information warfare, including its categories and strategies. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Cyber Kill Chain, TTPs, Behaviors, and Threat Hunting
If you know how most threat actors and groups attack their targets, you'll be better equipped to defend against those attacks. In this course, you'll explore the seven phases of the Cyber Kill Chain, which aims to guide defenders in their understanding of commonly used attack strategies. Next, you'll learn how tactics, techniques, and procedures can help you better understand the threats your organization faces. You'll move on to examine behavioral patterns typical with today's threat actors and advanced persistent threats. The average time it takes to detect a breach is around 200 days, which is why threat hunting has become a standard security practice. To complete this course, you'll explore threat hunting and its usefulness, as well as the concept of indicators of compromise (IoC). This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Risk Management, Cyber Threat Intelligence, and Threat Modeling
At the end of the day, cybersecurity is all about understanding risk. In this course, you'll learn about how risk pertains to cybersecurity, risk levels, and how to use a risk matrix to visualize risk. You'll also examine the concept, practice, and phases of risk management, which can help you minimize the negative effects of risk. Next, you'll explore how using Cyber Threat Intelligence is a more proactive approach towards your cybersecurity defenses and the four types of CTI. Finally, you'll learn about using threat modeling to stop threats before they become security incidents and the five steps common to the threat modeling process. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Incident Management, ML, AI, and Regulations
A very important job that a cybersecurity professional will need to be familiar with is that of incident management. In this course, you'll explore incident management and what it's designed to accomplish. Next, you'll examine the nine steps of the incident handling and response process to help familiarize yourself with the actions and expectations you may need to take to properly deal with a security incident. You'll learn about effective tools for protecting against advanced threats, as well as the role artificial intelligence and machine learning play in the current cybersecurity battlefield. Finally, you'll examine standards, regulations, and laws that govern how computer systems must be secured and maintained. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Hacking Methodology, MITRE ATT&CK Framework, and Diamond Model
Being an ethical hacker means, in some ways, that you'll need to assume the identity of a unscrupulous hacker. In this course, you'll learn what it means to be a hacker, the common hacker classes, and the five phases of hacking. As an ethical hacker, you may encounter those that don't understand what that means and how a person can use seemingly dangerous skills towards an ethical purpose. You'll examine the MITRE ATT&CK framework designed to help organizations improve defenses by understanding the attacker's methods and creating effective mitigation strategies to counter them. You'll also explore the Diamond Model of intrusion analysis which is a framework used to analyze the various components of a cyber attack. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Footprinting, Google Dorks, Search Engines, and Subdomains
Knowledge is power and in the ethical hacking game, the more you know about your target, the more likely you are to find a weakness in their security. In this course, you'll explore the practice of footprinting and the different types of information you can gather in this initial stage of attack. Next, you'll examine Google Dorks and some of the useful advanced search features of the Google search engine. You'll learn how to use the Shodan, Censys, and Thingful search engines to find IoT and other Internet-connected hosts and services in order to see the larger attack surface of a target. Finally, you'll explore subdomains and how they can lead to compromise if not properly managed, as well as some tools that can help you enumerate a target's subdomains. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Recon Tools and Tactics
Having knowledge of a target's physical location can be useful for social engineering and physical security assessments. In this course, you'll explore tools and tactics used to learn a target's geographical location. Next, you'll examine how conducting Open Source Intelligence on social media sites can yield sensitive information through direct investigation or social engineering. You'll move on to learn how to utilize job posts and job boards to search out useful target info like what technologies are being used, names of legitimate users, and areas that may be weak due to lack of staffing. Finally, you'll explore the large portion of the Internet that consists of the dark and deep webs and how these mostly unseen resources can be used to discover potentially sensitive info about a target. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Footprinting and Social Engineering Recon and Countermeasures
If you're engaged in a security assessment, mapping your target's public network presence is a critical step in that process. In this course, you'll learn how to discover the public network information associated with your target using WHOIS and DNS services. Next, you'll explore a few commonly used footprinting tools that will help you with not only the exam, but in real life as well. You'll move on to examine how you can use social engineering techniques like shoulder surfing and dumpster diving to obtain useful or sensitive information about your target's organization. Finally, you'll learn about some security controls that could be recommended to a client to help them better protect against an attacker's footprinting and recon efforts. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Network Scanning, TCP, Host Discovery, and Port/Service Scanning
An ethical hacker can be most effective when employing the right tools for the job. In this course, you'll learn about networking scanning types and the various flags used in TCP communication. Next, you'll explore commonly used network scanning tools used by many of today's security professionals. You'll then move on to learn about tools that can be used for host discovery, common methods of implementation, and even some countermeasures for prevention purposes. Finally, you'll examine the differences between port and service scans, their use cases, and common port/service associations. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Nmap TCP Scans
When scanning a target with nmap for open ports and/or services, there are several common types of scans. In this course, you'll explore TCP Connect scans, how to issue a TCP Connect scan with nmap, and pros and cons of using this type of scan. You'll also look at Stealth and TCP scans, how to issue them with nmap, and their pros and cons. Next, you'll examine how good network security professionals employ firewalls to protect their assets and how this can hinder network-based recon activities. Finally, you'll learn about using nmap's ACK scan for the purposes of mapping possible firewall rules enumerating port states. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Nmap IDLE IPID, UDP, and SCTP Scans
Staying off of the radar of your target's security team is a common goal for many ethical hackers when performing security assessments. In this course, you'll learn to use the map IDLE IPID scan to take advantage of other network hosts to obfuscate scan origins from detection systems and logs. You'll explore using nmap to discover what is utilizing UDP to help you add to your list of possible inroads of a target system. You'll also examine how SCTP works and how to work with nmap to use it for scanning purposes. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Scan Optimization, OS Identification, and IDS/Firewall Evasion
Running nmap scans can sometimes take a lot of time. In this course, you'll explore a few options and techniques for decreasing the amount of time you wait for nmap to complete its scans. Knowing what operating system your target is running sets the stage for how you'll conduct the subsequent steps of your hacking methodology, so you'll also examine common tools and techniques for discovering a target's host OS. Finally, you'll learn about tactics and tools that can be used to help you evade common network security controls such as firewalls and intrusion detection systems (IDS). This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: NetBIOS, SMB, SNMP, and LDAP Enumeration
To be a successful ethical hacker, you need to be good at gathering information. In this course, you'll explore the concept of enumeration, including what it is, how it's done, and the importance of the details gathered during this process. Next, you'll learn how to enumerate a target's useful or sensitive information using both Server Message Block (SMB) and NetBIOS. You'll move on to learn how you can use Simple Network Management Protocol (SNMP) to access information about target systems. Finally, you'll explore the details of the Lightweight Directory Access Protocol (LDAP) protocol and some tools that use LDAP to help you enumerate your targets. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: NTP, NFS, SMTP, and FTP Enumeration
Having the correct time helps to ensure systems operate properly, especially if you have configured things like time-based access. In this course, you'll explore the Network Time Protocol (NTP), including attributes and enumeration tools. You'll also examine the Network File System (NFS) and how it can be taken advantage of when implemented incorrectly. Finally, you'll learn about the Simple Mail Transfer Protocol (SMTP) and File Transfer Protocol (FTP), including what details can be enumerated from target systems using both of these protocols. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Vulnerability Assessment, Management, and Classification
One of the main job duties of many ethical hackers is performing vulnerability assessments. In this course, you'll explore the basic concepts of vulnerability assessments, as well as tools and resources commonly used when performing one. You'll examine the vulnerability management life cycle and its common activities. Finally, you'll learn about the various vulnerability types you may discover during an assessment. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Vulnerability Assessment Types, Models, Tools, and Reports
Performing a vulnerability assessment allows you to locate potential weaknesses in systems, networks, and channels of communication. This is a vital step in defending systems against attacks. In this course, you'll learn about the different types of vulnerability assessments. You'll move on to explore various vulnerability assessment models and tools. Finally, you examine important information that should be included in your vulnerability assessment reports. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Windows Authentication
When it comes to ethical hacking, repeatable successful tactics and processes, as well as secure authentication, are the name of the game. In this course, you'll learn about Windows authentication methods and the process behind them. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Passwords Attacks, Extraction, and Cracking
Passwords are a part of many of today's authentication systems and are therefore prone to attack. In this course, you'll investigate common attack methods and tools used to defeat passwords. You'll examine how hackers are able to obtain and decrypt a user's password, including tools and techniques used to procure encrypted passwords and cracking tools used to uncover the original password data. Finally, you'll learn about common password cracking enhancement techniques aimed to decrease the amount of time and increase the success rate when attempting to crack passwords. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Buffer Overflows, Privilege Escalation, and System Access
Buffer overflows can be one of the more mysterious and difficult techniques to understand and employ, but when successful they can be highly useful when gaining access to target systems. In this course, you'll explore the basic concepts behind buffer overflows, as well as some useful protections against them and how to develop and deploy them in a test environment. Next, you'll examine common privilege escalation techniques, for both Windows and Linux operating systems, that can help you obtain full administrative access. Once you've fully compromised a host, you're going to want to hang on to that access for a long as possible. Finally, you'll learn about tools and techniques that will help you maintain access over a compromised target system. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Steganography and Avoiding Detection
Exfiltration of sensitive data is a common goal of many hacks. In this course, you'll explore how hackers are able to avoid detection when exfiltrating data by using steganography techniques and tools. On average it takes roughly nine months before a breach is detected. You'll also examine common tactics attackers use to cover their tracks and avoid detection by administrators. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: AD Enumeration, Mimikatz, and Pivoting Techniques
Enumerating the Active Directory (AD) during a pentest is important to identify vulnerabilities and attack vectors that may be used to gain unauthorized access to the network. In this course, you will learn about enumeration tools that can help to identify misconfigurations or policy violations that may put the organization at risk. You'll explore how the mimikatz tool is used to extract sensitive information - such as authentication credentials - from a computer system's memory to test its security. Next, explore how pivoting is used to gain access to other systems within a network and learn about tools and techniques used for pivoting by ethical hackers. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Malware, Threats, Trojans, and Viruses
Malware is a common threat used to attack, compromise, and even destroy computer systems. In this course, you'll learn about common malware types and components so you can properly defend against malicious software. Then, you'll move on to explore advanced persistent threats (APTs), which are becoming more and more of a danger due to their sophisticated malware. You'll examine the malicious software version of the Trojan Horse, as well as the different types of Trojans, deployment methods, construction, and techniques for evading antivirus detection. Finally, you'll learn about viruses and worms, including concepts, types, and characteristics. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Fileless Malware, Malware Analysis, and Countermeasures
The most common way for antivirus programs to detect a malware infection is by checking files against a database of known malicious objects. In this course, you'll learn about fileless malware, which avoids detection by not writing any files with known malicious content. Next, you'll explore malware analysis techniques that allow you to configure stronger defenses. You'll also examine sheep dipping and how to build a test environment. There are many security controls to protect against malware infections, so you'll complete this course by learning about countermeasures like logging, antivirus, and backups. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Sniffing and Poisoning
Networks are constantly sending data to deliver messages and keep network services working, but those data packets may contain sensitive information like passwords. In this course, you'll examine how an attacker can gain access to sensitive data through packet sniffing. You'll learn how attackers can manipulate Dynamic Host Configuration Protocol (DHCP), which can allow them to then intercept target host communications. Next, you'll explore how attackers can manipulate Address Resolution Protocol (ARP) by taking advantage of the default functions of ARP. You'll move on to examine how attackers trick users into sharing personal information through domain name system (DNS) poisoning. Finally, you'll learn about common security controls that allow networks to communicate, while still adding layers of scrutiny, control, and obfuscation. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Social Engineering, Insider Threats, and Identity Theft
Often times, the most insecure point in a network is not the network hosts, but the end user that works with it. In this course, you'll explore the concepts and tactics of social engineering attacks, where the end user becomes the vulnerable system. The most dangerous attack can come from inside your network. You'll also examine insider threats, including why they're effective, their organization impacts, and why they're difficult to detect and defend against. Identity theft is one of the most common and lucrative avenues of attack. To complete this course, you'll learn the basic concepts, motives, and goals behind identity theft attacks. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: DoS, DDoS, Volumetric, and Protocol Attacks
Denial-of-service (DoS) attacks can be very disruptive to an organization both monetarily and reputationally. In this course, you'll explore denial-of-service and distributed denial-of-service (DDoS) attacks, as well as common DoS techniques and categories and common tools used to perform them. Next, you'll examine volumetric DoS attacks, which are one of the more common types deployed by attackers. These include UDP flood, Ping of Death, Smurf, and Pulse Wave. Finally, you'll learn about protocol-based DoS attacks, including SYN floods, ACK floods, and fragmentation attacks. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: App Layer Attacks, Botnets, and DoS Countermeasures
The application layer is another prime target for denial-of-service (DoS) attacks. In this course, you'll explore common application layer DoS attacks like SlowLoris, the Reddit Hug of Death, and UDP app-layer attacks. With botnet traffic making up about 25% of all Internet traffic, they are a real cause for concern. You'll also learn about bots and botnets, including their purpose and common ways they are proliferated. Since DoS attacks can cause so much havoc, you need to do all you can to defend against them. Finally, you'll explore commonly deployed DoS and distributed denial-of-service (DDoS) defensive countermeasures, tools, and strategies. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Hijacking Concepts and Countermeasures
Sessions are like a verified conversation between trusted systems, which makes session hijacking a common form of attack. In this course, you'll learn about session hijacking, including how it's accomplished and the different types. Session hijacking attacks can be performed at the network level, so you'll also explore common network-based session hijacking attacks such as UDP, TCP, and RST hijacking. Next, you'll move on to examine common application level session hijacking attacks such as man-in-the-middle, man-in-the-browser, cross-site scripting, and cross-site request forgery. Finally, you'll learn about common session hijacking security controls and countermeasures, as well as best practices like using encrypted protocols and secure session handling techniques. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Intrusion Detection and Prevention, Firewalls, and Honeypots
Intrusion detection and prevention systems are security controls that provide alerts and protection for many organizations today. In this course, you'll explore their function, commonly deployed IDS/IPS solutions, and techniques for evading detection by these systems. Next, you'll examine firewalls, their role as a security countermeasure, and techniques commonly used to bypass them. If you know how an attacker is likely to attack, you can build better defenses to protect your organization. Finally, you'll learn how honeypots can be used to determine the attacks a production network is most likely to face from threats. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Web Server Hacking, Attacks, and Attack Methodologies
Having a web presence is almost a necessity in today's business age, but web applications can be very complicated and difficult to build securely. This includes the web server that runs the app. In this course, you'll explore the web server, its function, common components that can lead to vulnerabilities, and security controls to help mitigate those possible vulnerabilities. Next, you'll examine common web server attacks such as directory traversal, HTTP response splitting, and Server-side Request Forgery (SSRF). Finally, you'll learn how following an established attack methodology will increase your likelihood of success when attacking a web server, and examine a common web server attack methodology and tools and techniques used at each step. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Web Application Attacks and Vulnerabilities
Web applications are typically the face of most organizations today. It's how customers interact with an organization's services, which makes for an inviting target for attackers. In this course, you'll examine the details of web applications, including their commonly used technologies, associated risks, and defenses. Next, you'll explore the OWASP Top 10 Web Application Attacks document, one of the best resources for understanding web application security vulnerabilities, and learn how to use common attacks as ethical hackers and protect against them as defenders. Finally, you'll learn about unvalidated redirects and forwards and how they can be used to access protected data. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Web App Hacking Methodology, CSRF Attacks, and Input Filter Evasion
Common attack vectors such as cross-site scripting are becoming more difficult to exploit due to the implementation of defenses. The key to success when security testing a web application is making sure you have an effective plan. In this course, you'll explore the common web app hacking methodology, as described by EC-Council. Next, you'll learn how the tools you have at your disposal will be crucial to your success when testing the security of any web application. You'll examine how CSRF attacks work, how to recognize them, and how to evade input filters to gain cross-site scripting (XSS) execution. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: IDOR Attacks, File Inclusion Attacks, Web APIs, and Webhooks
Direct Object Reference and Local and Remote File Inclusion attacks can prove very harmful to web applications. In this course, you'll examine how these attacks work and how to recognize them. First, you'll learn about Insecure Direct Object Reference (IDOR) attacks, including how to find and exploit them. Next, you'll learn about Local File Inclusion (LFI) and Remote File Inclusion (RFI) attacks, including how they work and how they can be leveraged to gain access to a remote system. Many of today's web applications utilize an application programming interface (API) to facilitate interaction between clients and services. To wrap up this course, you'll learn about attributes of APIs, how they compare with webhooks, and common vulnerabilities and security countermeasures associated with both APIs and webhooks. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: SQL Injection Concepts and Attacks
Many web applications store data in a back-end database and the data is then retrieved as the end user requests it from the front end. This process can allow for end-user injection of SQL queries, revealing sensitive data to the unauthorized attacker. In this course, you'll learn about SQL injection, including attack types, tools, security controls, and defense evasion techniques. Next, you'll explore error-based SQLi and how to test for and exploit this common SQLi vulnerability. SQL injections can be used to gain access to sensitive information or even allow access into a remote system, but they aren't always easily executed. To complete this course, you'll learn about blind-based SQLi methods and how to use them to access sensitive information on a remote system. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: SQL Injection and SQLMap
SQL injection (SQLi) is typically used to access sensitive information from a target's database, but under the right circumstances, it can be used to access the remote file system or even allow for remote system shell access. In this course, you'll learn the SQLi techniques used to read and write to files on the target system, as well as gain interactive shell access. Manual SQL injection testing is a necessary skill, but often time to test is limited and it's useful to have a tool like SQLMap. You'll finish this course by learning how to use SQLMap to automate the process of testing SQL injections. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Wireless Concepts, Threats, and Hacking Tools
Wireless technologies abound in today's networks, making them a prime target for attack. In this course, you'll explore the features of Wi-Fi, common standards, authentication types, antennas, and encryption schemes. Next, you'll examine common threats against wireless technologies that you need to be aware of to be an effective security professional, including authentication attacks, evil twins, rogue access point (rogue AP), and denial-of-service (DoS). To complete this course, you'll learn about commonly used wireless hacking tools, including those used for discovery, mapping, traffic analysis, and wireless attacks. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Wireless Hacking and Countermeasures
There are a few common attack vectors when targeting Wi-Fi networks that you should be aware of. In this course, you'll learn how to perform wireless hacking attacks such as Media Access Control (MAC) spoofing, deauthentication, and WPA/2 encryption cracking. Defending wireless networks can be a daunting task if you're unaware of effective security countermeasures. To complete this course, you'll explore common security controls that will get you on the right track to keeping your wireless network safe. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Mobile Hacking, OS Security, and Device Management
Mobile devices are one of the core components of today's network environments, so it's vital to know how and where they are possibly vulnerable. In this course, you'll explore the attack surface related to mobile devices and the Top 10 Mobile Risks as defined by OWASP, in terms of both attacking and defending these critical pieces of infrastructure. Next, you'll examine common vulnerabilities and attack tools for both Android and iOS, as well as defensive measures you can take to secure them. One of the main reasons that attackers are successful against mobile devices is due to the difficulty in managing them. To complete this course, you'll learn about the need for mobile device management software, how to deploy it, and how it helps secure things in a BYOD world. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: IoT Threats, Vulnerabilities, Attack Tools, and Countermeasures
Internet of Things (IoT) devices make our lives convenient and that makes them more prevalent every day. In this course, you'll learn about IoT and its main components, as well as IoT architecture, deployment areas, protocols, communication models, and security challenges. The best way to effectively attack IoT devices is to be familiar with the common threats and vulnerabilities, so next you'll explore these areas. Finally, you'll examine common attacks and hacking tools that you can use to gain access to IoT devices, as well as defensive countermeasures you can employ to protect against those attacks and tools. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Operational Technology Concepts, Attack Tools, and Countermeasures
To be effective at both defending and attacking operational technology (OT) systems, you must first be aware of the basic components and concepts that OT systems are made of. In this course, you'll explore OT systems and their base components, as well as systems such as industrial control system (ICS), Supervisory Control and Data Acquisition (SCADA), programmable logic controllers, and Intelligent Electronic Devices (IED). You'll also learn about the common security challenges facing OT systems. Finally, you'll examine common OT-related attacks, tools, and defensive countermeasures. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Cloud Computing, Containers, Hacking, and Security Controls
Many of today's systems are becoming cloud-based at a rapid pace. In this course, you'll explore different cloud services, deployment models, responsibility areas, and architectures relevant to your CEH exam. Another rapidly adopted technology in today's networks is containers, making knowledge of them a necessary skill. You'll examine containers, technologies like Docker, and orchestration, as well as common security challenges. Next, you'll learn why cloud services have been prone to security issues and breaches and examine common security vulnerabilities and assessment tools. Finally, you'll learn about common security controls for cloud environments that can help you protect cloud accounts, storage, containers, and orchestration. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: Cryptography, Algorithms, Implementations, and Tools
Encryption is one of the best security controls available for defending computer networks and data, and cryptography plays a vital role in this process. In this course, you'll explore cryptography, including its purpose, types, and common ciphers, to help you better understand the strengths and weaknesses of common crypto-systems. Next, you'll examine the common algorithms and implementations used by various crypto-systems, including symmetric and asymmetric algorithms, hashing functions, and digital signatures. Encryption is highly effective for protecting sensitive data, but how do you encrypt something? To complete this course, you'll learn about tools that can help you secure sensitive data on servers, desktops, e-mail, and mobile. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
CEH v12: PKI, Cryptanalysis, and Attack Countermeasures
In today's day and age, data must be encrypted for secure communication with third parties. But how is this accomplished? In this course, you'll examine public key infrastructure (PKI) as an encryption solution. You'll also explore PKI components, processes, and how it compares with self-signed certificates. As long as there has been encrypted data, there have been attempts to break those encryptions. You'll next learn about cryptanalysis methods and attacks used to reveal hidden messages. Finally, you'll explore how to deploy the right encryption in the right way by learning about best practices and strategies for keeping your data safe. This course is one in a series that helps to prepare you for the Certified Ethical Hacker v12 (312-50) exam.
Course options
We offer several optional training products to enhance your learning experience. If you are planning to use our training course in preperation for an official exam then whe highly recommend using these optional training products to ensure an optimal learning experience. Sometimes there is only a practice exam or/and practice lab available.
Optional practice exam (trial exam)
To supplement this training course you may add a special practice exam. This practice exam comprises a number of trial exams which are very similar to the real exam, both in terms of form and content. This is the ultimate way to test whether you are ready for the exam.
Optional practice lab
To supplement this training course you may add a special practice lab. You perform the tasks on real hardware and/or software applicable to your Lab. The labs are fully hosted in our cloud. The only thing you need to use our practice labs is a web browser. In the LiveLab environment you will find exercises which you can start immediately. The lab enviromentconsist of complete networks containing for example, clients, servers,etc. This is the ultimate way to gain extensive hands-on experience.
Sign In
WHY_ICTTRAININGEN
Via ons opleidingsconcept bespaar je tot 80% op trainingen
Start met leren wanneer je wilt. Je bepaalt zelf het gewenste tempo
Spar met medecursisten en profileer je als autoriteit in je vakgebied.
Ontvang na succesvolle afronding van je cursus het officiële certificaat van deelname van Icttrainingen.nl
Krijg inzicht in uitgebreide voortgangsinformatie van jezelf of je medewerkers
Kennis opdoen met interactieve e-learning en uitgebreide praktijkopdrachten door gecertificeerde docenten
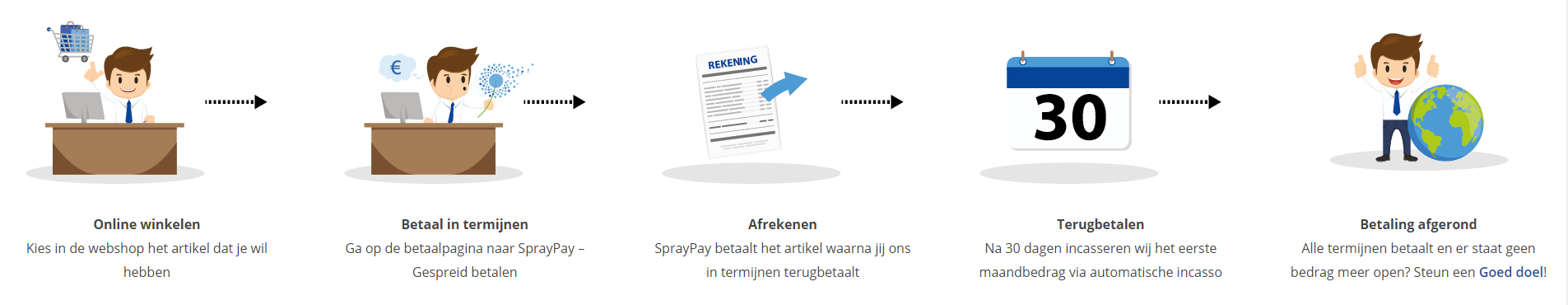
Orderproces
Once we have processed your order and payment, we will give you access to your courses. If you still have any questions about our ordering process, please refer to the button below.
read more about the order process
Een zakelijk account aanmaken
Wanneer u besteld namens uw bedrijf doet u er goed aan om aan zakelijk account bij ons aan te maken. Tijdens het registratieproces kunt u hiervoor kiezen. U heeft vervolgens de mogelijkheden om de bedrijfsgegevens in te voeren, een referentie en een afwijkend factuuradres toe te voegen.
Betaalmogelijkheden
U heeft bij ons diverse betaalmogelijkheden. Bij alle betaalopties ontvangt u sowieso een factuur na de bestelling. Gaat uw werkgever betalen, dan kiest u voor betaling per factuur.

Cursisten aanmaken
Als u een zakelijk account heeft aangemaakt dan heeft u de optie om cursisten/medewerkers aan te maken onder uw account. Als u dus meerdere trainingen koopt, kunt u cursisten aanmaken en deze vervolgens uitdelen aan uw collega’s. De cursisten krijgen een e-mail met inloggegevens wanneer zij worden aangemaakt en wanneer zij een training hebben gekregen.
Voortgangsinformatie
Met een zakelijk account bent u automatisch beheerder van uw organisatie en kunt u naast cursisten ook managers aanmaken. Beheerders en managers kunnen tevens voortgang inzien van alle cursisten binnen uw organisatie.
What is included?
| Certificate of participation | Yes |
| Monitor Progress | Yes |
| Award Winning E-learning | Yes |
| Mobile ready | Yes |
| Sharing knowledge | Unlimited access to our IT professionals community |
| Study advice | Our consultants are here for you to advice about your study career and options |
| Study materials | Certified teachers with in depth knowledge about the subject. |
| Service | World's best service |
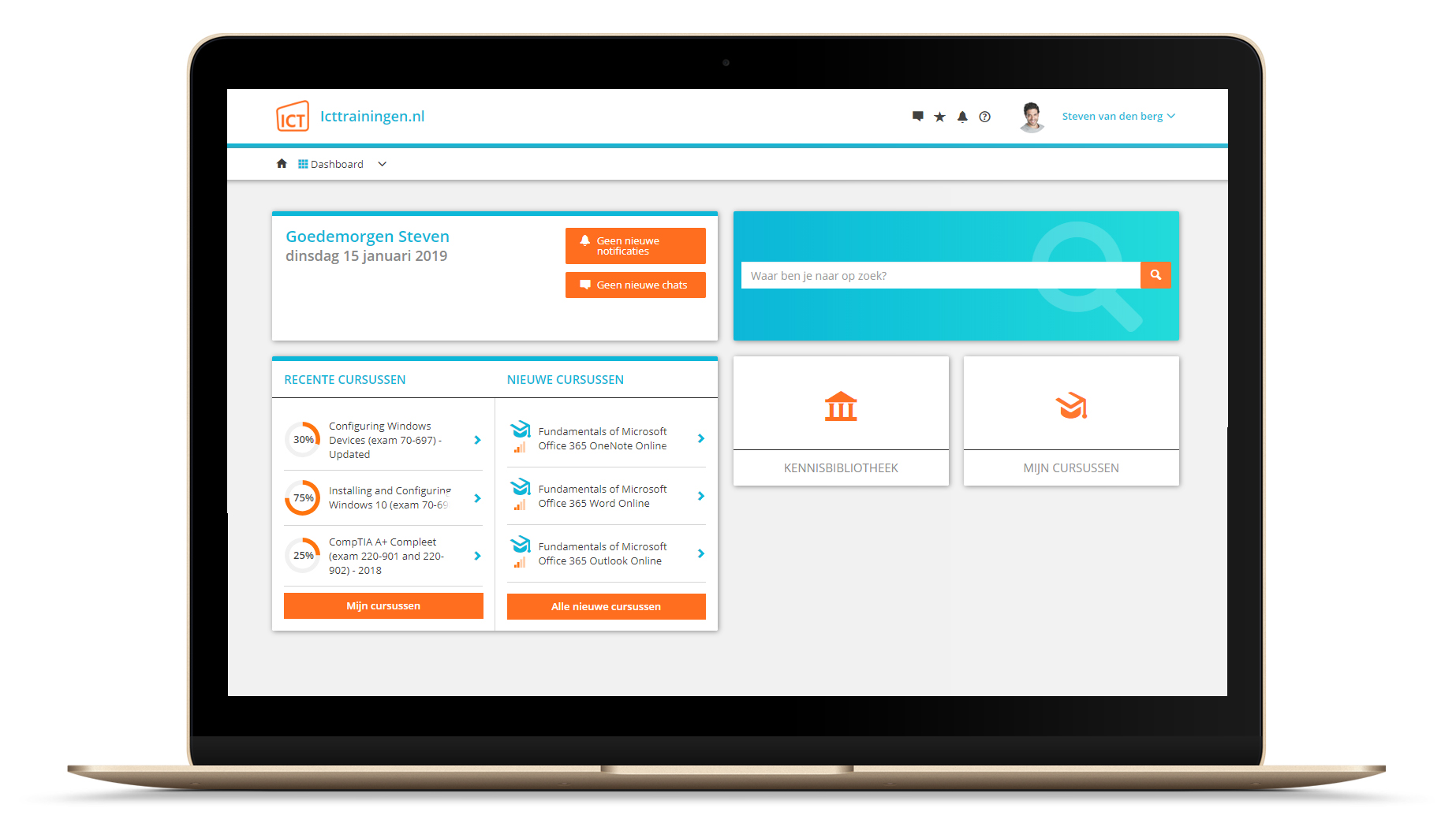
Platform
Na bestelling van je training krijg je toegang tot ons innovatieve leerplatform. Hier vind je al je gekochte (of gevolgde) trainingen, kan je eventueel cursisten aanmaken en krijg je toegang tot uitgebreide voortgangsinformatie.
FAQ
Niet gevonden wat je zocht? Bekijk alle vragen of neem contact op.