Course: Certified Information Security Manager (CISM) 2022
duration: 33 hours |
Language: English (US) |
access duration: 180 days |

Details
Are you an information security manager or is this part of your responsibilities? Then this training is suitable for you! CISM® is a globally recognized title for Information Security Management. With this title you increase your market value. During this online CISM® training you will be trained to become a broadly-educated specialist in the field of security management. After following this training you will be optimally prepared for the CISM® exam.
This training elaborates on the four CISM® knowledge domains:
- Information Security Governance.
- Information Security Risk Management.
- Information Security Program.
- Incident Management.
In this CISM® training course, you will learn about various standards and regulations in the field of IT security and how they influence an organisation's IT security decisions. In Risk Management, you will look at different analyses, such as SWOT and gap, and work with a risk register. You will explore concepts, such as hashing and encryption, to make the transition of data as secure as possible. Which role IPv4 and IPv6 can play in this and how to arrange authentication and authorisation securely.
You will also learn how to work securely with Windows and Linux cloud-based servers, both on-premises and remotely. Also covered is how to regularly test and evaluate your IT security. You will look at digital evidence, its collection, what techniques you can use for this and what restrictions are attached to it.
It is also important that business processes are not interrupted by IT problems. You will learn how to minimise the impact of disruptions and how to prepare for possible future problems/threats.
Result
After completing this training, you will have a knowledge of the four CISM® knowledge domains in order to be able to apply them in practice and you will be prepared for the international CISM® exam.
Prerequisites
You have a background and several years of experience in security- and/or information management. Please note: CISM certification requires at least five years of relevant work experience in at least two of the CISM domains.
Target audience
Security Specialist
Content
Certified Information Security Manager (CISM) 2022
CISM 2022: Information Security Governance
The best way to improve the enterprise security stance is to align IT security solutions with business objectives. In this course, you will consider how information security must align with business strategies. You will explore the business model for information security and review the importance of identifying and classifying assets critical to a business. Next, you will learn about supply chain security, personnel management, and the components of an information security program. You will discover the relationship between service-level agreements (SLAs) and organizational objectives and discuss the relevance of change and configuration management. Then, consider how to develop organizational security policies. Lastly, explore expense types, chain of custody, organizational culture, and how the Control Objectives for Information Technologies (COBIT) framework applies to IT governance. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Business Continuity & Security
Keeping business processes up and running is a priority for every type of business. Security plays an important role in the success of business continuity planning. In this course, you will discover the characteristics that define a business impact analysis (BIA) and explore disaster recovery plans (DRPs) and various data and IT security roles commonly present in an enterprise. Next, you will learn how contractual obligations can necessitate security compliance and audits. You will discover the importance of establishing performance and security baselines on-premises and in the cloud. Lastly, you will explore physical security and security control types with a slant on business process alignment. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Incident Response
Incident response is initiated when a security incident is confirmed. Incident response plan participants must know their roles and plan details for effectively minimizing the impact of security incidents. In this course, you will explore the components that make up an incident response plan, including roles, escalation procedures, and communication plans. Next, focus on incident escalation where applicable, incident eradication according to planned procedures, and incident containment to prevent further incident damage. Then discover the importance of analyzing past incident responses in the spirit of constant improvement and the reduction of incident response times. Lastly, find out how incident detection and automated responses are possible in the cloud. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Security Standards
Global and local security standards, including laws and regulations, are an important input to determine how enterprises deploy and manage security controls. In this course, you will learn how the European Union's General Data Protection Regulation (GDPR) data privacy legislation applies to any organization world-wide handling private EU citizen data. Next, you will explore various International Organization for Standardization/International Electrotechnical Commission (ISO/IEC) standards for proper data governance, followed by American data privacy and cloud security standards such as Health Insurance Portability and Accountability Act (HIPAA) and Federal Risk and Authorization Management Program (FedRamp). Discover how to secure cardholder data as related to Payment Card Industry Data Security Standard (PCI DSS) international security standards and review other data privacy legislation including Canada's Personal Information Protection and Electronic Documents Act (PIPEDA) and China's Personal Information Protection Law (PIPL). Lastly, explore the importance of securing cloud service usage in alignment with the Cloud Controls Matrix (CCM). This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Managing Risk
Residual risk remains after security controls are put in place to mitigate the impact of threats. The organizational appetite for risk determines what level of residual risk is acceptable. In this course, you will explore how risk management improves business operations by minimizing the impact of realized threats. You will learn how to calculate the cost of mitigating risk compared to the value of the protected asset and determine the cost-benefit analysis and return on investment when implementing security controls. Next, discover the importance of risk assessments, especially where there are changes to some aspect of the business or a specific business process. You will then explore how various risk approaches, such as risk acceptance, avoidance, transfer, and reduction, apply to an organization's tolerance of residual risk. Lastly, discover how risk heat maps are an effective method for communicating various degrees of risk. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Data Privacy
Enterprises must comply with relevant laws and regulations related to data privacy. This requires recognizing applicable laws and regulations and implementing the appropriate security controls. In this course, you will explore examples of personally identifiable information (PII) and protected health information (PHI) and learn about data residency implications related to the physical storage location of sensitive data. Next, learn how to reduce the possibility of data exfiltration through data loss protection policies and how to discover and classify data using Amazon Macie and Microsoft Purview governance. Then you will learn to configure data classification on the Microsoft Windows server platform and tag cloud resources for classification purposes. Lastly, explore how to configure Microsoft Azure storage account encryption using a customer-managed key. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Assessing Risk
Assessing risk is a crucial activity that enables organizations to evaluate risk exposure for business processes and assets. In this course, you will begin by exploring how to conduct vulnerability assessments and how the results can shed light on security control deficiencies. Next, you will learn how to perform a network vulnerability assessment and review the results, followed by scanning a web application for web app-specific vulnerabilities. You will discover how to conduct a gap analysis to determine the current security posture compared to a desired security posture. Then, you will explore the important aspects of when and how to run penetration tests. Lastly, you will see how to configure Microsoft Azure Policy assignments to determine cloud resource configuration compliance. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Managing Authentication
Strong authentication, such as with multi-factor authentication (MFA), ensures that devices, software, and users get legitimate access to resources. The omission of strong authentication configurations may result in successful brute force credential attacks. In this course, you will begin with a discussion of authentication categories and how they strengthen device, software, and user sign-in procedures. Next, you will learn to manage Amazon Web Services (AWS) and Microsoft Azure users and groups in the cloud followed by managing on-premises users and groups on the Windows and Linux platforms. You will then configure MFA for an AWS Identity and Access Management (IAM) user account and test MFA login. Lastly, you will learn how to harden user login security through password policies and how identity federation works. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Implementing Access Control
Authorization allows limited access to resources only after successful authentication. Resources can include IT services such as applications, databases, files, and folders, among others. In this course, explore the role authorization plays in allowing resource access and the various access control models used to ensure least privilege. Next, learn how to configure ABAC through Microsoft Dynamic Access Control, create an Azure dynamic group in the cloud, and use RBAC to grant permissions to Azure cloud resources. Finally, discover how to manage permissions for Windows and Linux-based file systems, handle Windows NTFS file system auditing, and configure Microsoft Active Directory delegated administration. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Network Security
Organizations should secure resource access while remaining compliant with relevant laws and regulations. One of the many ways to do this is to ensure proper network security controls are in place and reviewed regularly. In this course, examine the OSI model layers and their relevance to network security controls, as well as the security aspects of network switching and network access control. Next, explore DHCP and DNS security issues and Wi-Fi authentication methods, and discover how to harden a DHCP and DNS deployment on Windows Server. Finally, learn the importance of using honeypots and honeynets, and how to implement a honeypot and analyze captured network traffic. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Network Attack Mitigation
To effectively defend against common network attacks, organizations must truly understand how they are executed. Thereafter, information security managers can implement and manage security controls to address network security control objectives. In this course, explore firewall types, configure the built-in Windows Defender Firewall, and adjust firewall rules on a Linux host. Next, learn how to manage Azure cloud network security groups to control virtual network subnet and interface traffic and how forward and reverse proxy servers can enable inbound and outbound network security. Finally, examine the relevance of intrusion detection placement and prevention configurations and configure the open-source Snort IDS tool to detect suspicious traffic. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: IT Service & Data Availability
Ensuring IT service and data high availability can reduce downtime and increase business productivity. The configurations put in place to achieve high availability align with standard business continuity requirements. In this course, you will discover the importance of high availability as it relates to business objectives. Begin by exploring load balancing as a method of optimizing application performance and availability. Next, you will learn how to deploy a cloud-based application load balancing solution. Examine various backup types such as differential and incremental, in order to adhere to the Recovery Point Objective (RPO). Then configure backup for Windows Server and for Microsoft Azure resources and find out how redundant array of inexpensive disks (RAID) levels apply to data availability and resiliency to disk failures. Finally, configure software RAID on the Windows and Linux platforms and enable availability in the cloud by enabling storage account and virtual machine replication. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Common Network Security Threats
Some security controls are very specific to the threat that they address. Information security managers must be well versed in common network security threats in order to minimize the impact of realized threats on business processes. In this course, you will start by exploring various types of threat actors and their motivation for attacking networks. You will review industry standards related to categorizing threats, including common vulnerabilities and exposures (CVEs), the MITRE ATT&CK knowledge base, and the OWASP Top 10 web application security attacks. Next, you will learn how bug bounties are paid by companies to ensure the utmost in security for their products, which can influence customer choices. You will discover how various types of network attacks are executed including Wi-Fi attacks, SYN flood attacks, buffer overflow attacks, advanced persistent threats (APTs), and distributed denial-of-service (DDoS) attacks. Lastly, you will see how VPN anonymizer solutions and the Tor web browser can be used for anonymous network connectivity for legitimate as well as illegal purposes. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Common Network Security Attacks
Security technicians can benefit significantly by executing network security attacks in a controlled environment. This allows for an in-depth periodic review of security control efficacy related to IT networks. In this course, you will discover how networks can be scanned by attackers seeking potentially vulnerable services using free tools such as Nmap. You will then explore how attackers can compromise a user web browser, how SQL injection attacks can reveal more information than intended by the app designer, and how to configure a reverse shell where the compromised station reaches out to the attacker station, often defeating standard firewall rule sets. Next, you will learn how to spoof network traffic and execute a distributed denial-of-service (DDoS) attack. Lastly, you will discover how to brute force a Windows remote desktop protocol (RDP) connection to gain access to a Windows host. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Cloud Computing & Coding
The use of cloud services is a form of outsourcing of IT service which also introduces an element of risk. Software developers can use on-premises as well as cloud-based services to create, test, and deploy software solutions. In this course, you will explore cloud deployment models including public, private, hybrid, and community clouds. You will then cover cloud computing service models, such as Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS), including where the security responsibility lies in each model. Next, you will explore various cloud-based security controls addressing a wide variety of cloud computing security needs. You will discover how to deploy a repeatable compliant cloud-based sandbox environment using Microsoft Azure Blueprints. Next, explore how security must be included in each software development life cycle (SDLC) phase as opposed to post-implementation. Finally, discover the importance of secure coding practices and how security must integrate with software development, testing, deployment, and patching. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Data Protection with Cryptography
Cryptography provides solutions for ensuring data privacy and integrity. Various firmware and software solutions protect data in transit and data at rest. In this course, you will explore the CIA security triad and how it relates to the organization's security program. You will then review various cryptography solutions and discuss data integrity to assure that tampering has not occurred. Next, you will learn how Hardware Security Module (HSM) appliances and Trusted Platform Module (TPM) firmware provide cryptographic services. You will see how Transport Layer Security (TLS) supersedes the deprecated Secure Sockets Layer (SSL) network security protocol suite followed by discussing virtual private network (VPN) encrypted network tunnels, and the IP Security (IPsec) network security protocol suite. Lastly, you will explore the PKI hierarchy and how public key infrastructure (PKI) certificates are used for digital security throughout the certificate life cycle. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Applied Cryptography
The periodic evaluation of the efficacy of cryptographic solutions is possible only with an understanding of how cryptography secures digital environments. In this course, you will explore data integrity by hashing files on the Linux and Windows platforms in an effort to detect unauthorized changes. You will configure a web application HTTPS binding to secure network communications to and from the web application. Then you will deploy a private certificate authority (CA), manage certificate templates, and deploy public key infrastructure (PKI) certificates. Next, you will configure a web application to require trusted client certificates. Finally, you will encrypt data at rest on Linux, on Windows with Encrypting File System (EFS), and Microsoft Bitlocker, and you will configure a cloud VPN connection and implement IPsec on Windows. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Secure Device & OS Management
IT departments must work in conjunction with higher-level management to determine when and how to securely use technological solutions that support the business strategy. In this course, begin by exploring how mobile device usage in a business environment can introduce risk and how that risk can be managed with centralized remote wipe capabilities. Then find out how Microsoft Intune can be used to centrally manage devices and how to securely wipe a disk partition. Learn how to harden Windows computers using Group Policy and disable the deprecated SSL network security protocol on Windows hosts. Next, investigate common digital forensics hardware and software solutions, as well as the storage area network (SAN) security and jump box solutions to manage hosts securely and remotely. Finally, discover how to manage Azure resources permissions using managed identities, examine device and OS hardening techniques, and investigate the importance of firmware and software patching. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Social Engineering & Malware
Modern day IT device users must have an awareness of the deception by malicious actors through their devices. Recurring security awareness training in an organization is by far the most effective way to minimize realized threats against business assets. In this course, you will explore social engineering in its various forms, focusing on malware types like viruses, trojans, and ransomware. Then you will review various examples of phishing email messages and find out how to detect that they are fraudulent. Next, you will use the Metasploit Framework's Social-Engineer Toolkit (SET) to execute a social engineering attack, discover how botnets work, and learn how their function can be mitigated. You will configure a Microsoft Windows virus and threat protection. Finally, you will upload an infected file to an online service for malware scanning. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
CISM 2022: Security Monitoring
Because today's business computing environments can contain a dizzying array of device types, centralized data ingestion, and analysis, looking for anomalies is a critical part of defending against technological threats. In this course, you will begin by reviewing Microsoft Defender for Cloud security recommendations in the Microsoft Azure cloud and monitoring the performance of Windows hosts. Then you will review, search, and filter Windows Event Viewer logs, configure Windows log forwarding to a second Windows host, and monitor the performance of a Linux host. Next, you will view various Linux logs, enable Linux log forwarding using syslog-ng, review web server logs, and monitor the performance of cloud services. Finally, you will learn how to decipher threat positives and negatives, how security information and event management (SIEM) and security orchestration, automation, and response (SOAR) can detect and remediate security incidents, and how to configure the Microsoft Sentinel SIEM. This course can be used to prepare for the Certified Information Security Manager (CISM) exam.
Course options
We offer several optional training products to enhance your learning experience. If you are planning to use our training course in preperation for an official exam then whe highly recommend using these optional training products to ensure an optimal learning experience. Sometimes there is only a practice exam or/and practice lab available.
Optional practice exam (trial exam)
To supplement this training course you may add a special practice exam. This practice exam comprises a number of trial exams which are very similar to the real exam, both in terms of form and content. This is the ultimate way to test whether you are ready for the exam.
Optional practice lab
To supplement this training course you may add a special practice lab. You perform the tasks on real hardware and/or software applicable to your Lab. The labs are fully hosted in our cloud. The only thing you need to use our practice labs is a web browser. In the LiveLab environment you will find exercises which you can start immediately. The lab enviromentconsist of complete networks containing for example, clients, servers,etc. This is the ultimate way to gain extensive hands-on experience.
Sign In
WHY_ICTTRAININGEN
Via ons opleidingsconcept bespaar je tot 80% op trainingen
Start met leren wanneer je wilt. Je bepaalt zelf het gewenste tempo
Spar met medecursisten en profileer je als autoriteit in je vakgebied.
Ontvang na succesvolle afronding van je cursus het officiële certificaat van deelname van Icttrainingen.nl
Krijg inzicht in uitgebreide voortgangsinformatie van jezelf of je medewerkers
Kennis opdoen met interactieve e-learning en uitgebreide praktijkopdrachten door gecertificeerde docenten
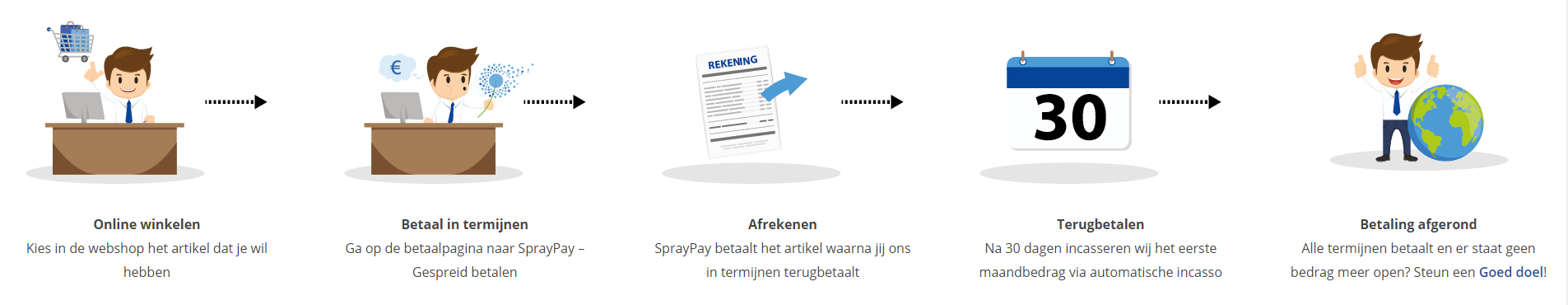
Orderproces
Once we have processed your order and payment, we will give you access to your courses. If you still have any questions about our ordering process, please refer to the button below.
read more about the order process
Een zakelijk account aanmaken
Wanneer u besteld namens uw bedrijf doet u er goed aan om aan zakelijk account bij ons aan te maken. Tijdens het registratieproces kunt u hiervoor kiezen. U heeft vervolgens de mogelijkheden om de bedrijfsgegevens in te voeren, een referentie en een afwijkend factuuradres toe te voegen.
Betaalmogelijkheden
U heeft bij ons diverse betaalmogelijkheden. Bij alle betaalopties ontvangt u sowieso een factuur na de bestelling. Gaat uw werkgever betalen, dan kiest u voor betaling per factuur.

Cursisten aanmaken
Als u een zakelijk account heeft aangemaakt dan heeft u de optie om cursisten/medewerkers aan te maken onder uw account. Als u dus meerdere trainingen koopt, kunt u cursisten aanmaken en deze vervolgens uitdelen aan uw collega’s. De cursisten krijgen een e-mail met inloggegevens wanneer zij worden aangemaakt en wanneer zij een training hebben gekregen.
Voortgangsinformatie
Met een zakelijk account bent u automatisch beheerder van uw organisatie en kunt u naast cursisten ook managers aanmaken. Beheerders en managers kunnen tevens voortgang inzien van alle cursisten binnen uw organisatie.
What is included?
| Certificate of participation | Yes |
| Monitor Progress | Yes |
| Award Winning E-learning | Yes |
| Mobile ready | Yes |
| Sharing knowledge | Unlimited access to our IT professionals community |
| Study advice | Our consultants are here for you to advice about your study career and options |
| Study materials | Certified teachers with in depth knowledge about the subject. |
| Service | World's best service |
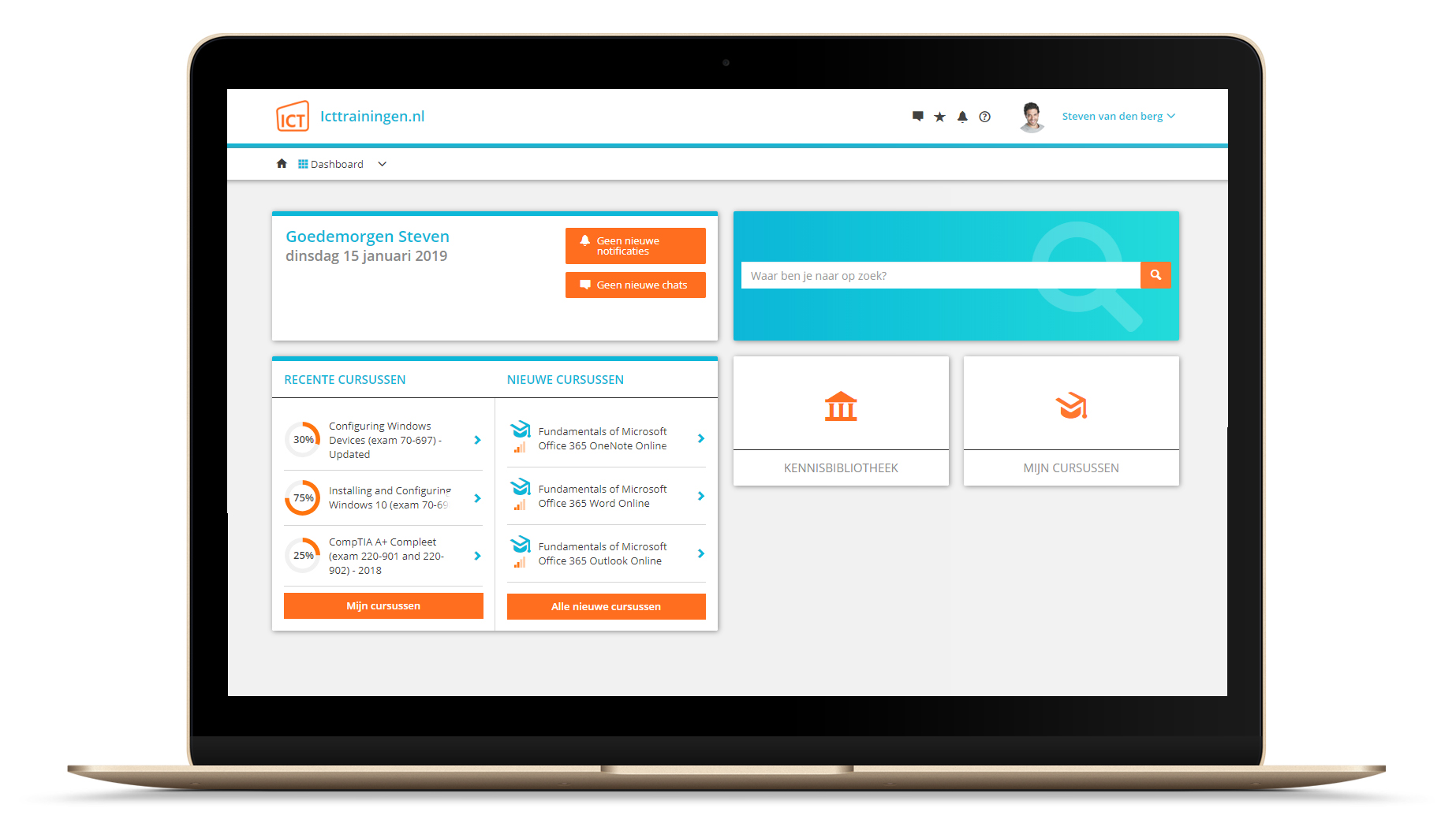
Platform
Na bestelling van je training krijg je toegang tot ons innovatieve leerplatform. Hier vind je al je gekochte (of gevolgde) trainingen, kan je eventueel cursisten aanmaken en krijg je toegang tot uitgebreide voortgangsinformatie.
FAQ
Niet gevonden wat je zocht? Bekijk alle vragen of neem contact op.