Course: Foundations of iOS Security
duration: 5 hours |
Language: English (US) |
access duration: 90 days |

Details
In this iOS Security training course you will learn the main features from the iOS security architecture. You will learn how to protect data in a IPhone, how you can protect iOS applications and enterprise devices, how to manage and design several iOS applications in fuzz tests. Finally you will learn the installation of jailbreaking tools and how to use them in iOS devices.
Among subjects that covered are return-oriented programming (ROP), VPN protocols, iOS 8 support, Mandatory code signing, OS X Server, ARM calling and far more.
Result
After completing this course you are familiar with the main features of the iOS security architecture.
Prerequisites
There is nog specific knowledge required.
Target audience
Security Specialist
Content
Foundations of iOS Security
iOS Security Architecture and Application Data Protection
- start the course
- describe how Apple protects the Apple Store
- define malware, exploitation, and compare Mac OS threats versus iOS threats
- describe reduced attack surface and stripped-down iOS
- describe code signing, return-oriented programming (ROP), and data execution prevention
- describe privilege separation, address space layout randomization, and sandboxing
- describe data protection API and class hierarchy
- describe file protection classes
- describe keychain item protection classes
- describe how file and keychain data protection classes are collected and managed in keybags
- describe how user passcodes may be attacked
- identify components of network security supported by iOS 8
- describe the VPN protocols and authentication methods supported by iOS 8
- describe Wi-Fi standards and authentication methods supported by iOS 8
- describe Bluetooth connections and profiles supported by iOS 8
- describe iOS 8 support for single sign-on authentication on enterprise networks
- describe iOS 8 support for AirDrop security
- describe how code signing is used to enforce iOS security
- describe how Mandatory Code Signing is controlled by the Mandatory Access Control Framework, including AMFI hooks
- describe the provisioning profile and how the provisioning file is validated
- use the Xcode codesign tool to show signing certificate authority information for an iOS application
- use command line to list the entitlements for a signed iOS application
- describe how application signing information can be collected and verified
- describe how signatures are enforced on application processes
- describe how to prevent signed code from being tampered with
- describe how to use Just-In-Time compiling to implement dynamic code signing
- use the Xcode codesign tool to obtain information on an iOS application's signing certificate authority and its granted entitlements
Securing Against Threats, Securing for Enterprise, and Jailbreaking Devices
- start the course
- identify iOS Sandbox components and describe how they are related
- describe how runtime process security makes use of sandboxing to protect applications and their data on iOS 8 devices
- describe how extensions are sandboxed to protect their files and memory space in iOS
- describe how applications are launched under a sandbox and how applications are restricted to their own container directories in the App Store
- identify the contents of a configuration profile and how to identify configuration profile payload types
- describe the general functionality of the Apple Configurator
- use Apple Configurator to create a new configuration profile
- use Apple Configurator to update and remove configuration profiles
- configure and run the Profile Manager service
- enroll a user device with the OS X Server mobile device management service using the user's Profile Manager web portal
- enroll a user device with the OS X Server mobile device management service by downloading and installing an enrollment profile
- describe the basic idea behind fuzzing and how it is used to reveal security issues in iOS applications
- describe steps for carrying out a fuzz test
- carry out a fuzz test on Safari web browser for Mac OS X Yosemite
- describe how to exploit use-after-free and double free bugs
- describe the concept of regions and how regions are allocated and deallocated
- describe TCMalloc allocator as well as large and small object allocation and deallocation
- describe background on ROP and basics in ARM architecture
- describe how system calls are invoked on ARM
- describe the ARM calling convention on iOS
- create a new configuration profile using Apple Configurator and enroll a device using the OS X Profile Manager service
Course options
We offer several optional training products to enhance your learning experience. If you are planning to use our training course in preperation for an official exam then whe highly recommend using these optional training products to ensure an optimal learning experience. Sometimes there is only a practice exam or/and practice lab available.
Optional practice exam (trial exam)
To supplement this training course you may add a special practice exam. This practice exam comprises a number of trial exams which are very similar to the real exam, both in terms of form and content. This is the ultimate way to test whether you are ready for the exam.
Optional practice lab
To supplement this training course you may add a special practice lab. You perform the tasks on real hardware and/or software applicable to your Lab. The labs are fully hosted in our cloud. The only thing you need to use our practice labs is a web browser. In the LiveLab environment you will find exercises which you can start immediately. The lab enviromentconsist of complete networks containing for example, clients, servers,etc. This is the ultimate way to gain extensive hands-on experience.
Sign In
WHY_ICTTRAININGEN
Via ons opleidingsconcept bespaar je tot 80% op trainingen
Start met leren wanneer je wilt. Je bepaalt zelf het gewenste tempo
Spar met medecursisten en profileer je als autoriteit in je vakgebied.
Ontvang na succesvolle afronding van je cursus het officiële certificaat van deelname van Icttrainingen.nl
Krijg inzicht in uitgebreide voortgangsinformatie van jezelf of je medewerkers
Kennis opdoen met interactieve e-learning en uitgebreide praktijkopdrachten door gecertificeerde docenten
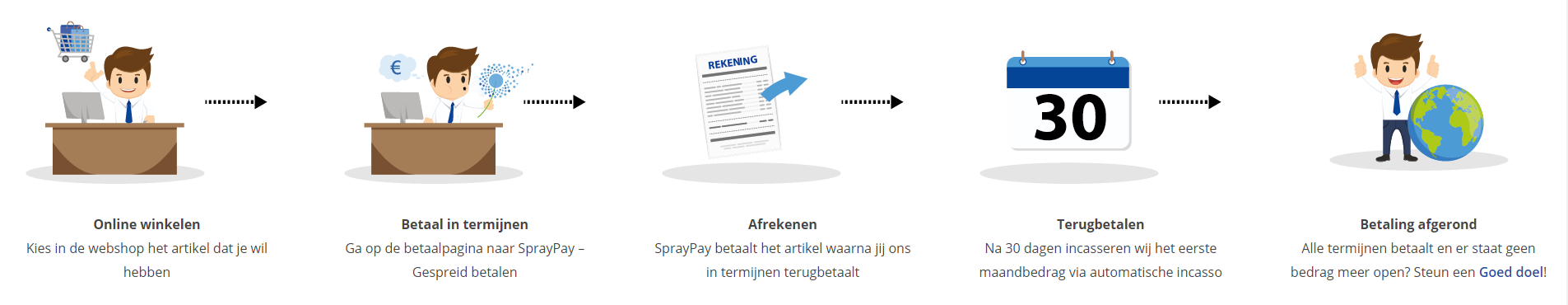
Orderproces
Once we have processed your order and payment, we will give you access to your courses. If you still have any questions about our ordering process, please refer to the button below.
read more about the order process
Een zakelijk account aanmaken
Wanneer u besteld namens uw bedrijf doet u er goed aan om aan zakelijk account bij ons aan te maken. Tijdens het registratieproces kunt u hiervoor kiezen. U heeft vervolgens de mogelijkheden om de bedrijfsgegevens in te voeren, een referentie en een afwijkend factuuradres toe te voegen.
Betaalmogelijkheden
U heeft bij ons diverse betaalmogelijkheden. Bij alle betaalopties ontvangt u sowieso een factuur na de bestelling. Gaat uw werkgever betalen, dan kiest u voor betaling per factuur.

Cursisten aanmaken
Als u een zakelijk account heeft aangemaakt dan heeft u de optie om cursisten/medewerkers aan te maken onder uw account. Als u dus meerdere trainingen koopt, kunt u cursisten aanmaken en deze vervolgens uitdelen aan uw collega’s. De cursisten krijgen een e-mail met inloggegevens wanneer zij worden aangemaakt en wanneer zij een training hebben gekregen.
Voortgangsinformatie
Met een zakelijk account bent u automatisch beheerder van uw organisatie en kunt u naast cursisten ook managers aanmaken. Beheerders en managers kunnen tevens voortgang inzien van alle cursisten binnen uw organisatie.
What is included?
| Certificate of participation | Yes |
| Monitor Progress | Yes |
| Award Winning E-learning | Yes |
| Mobile ready | Yes |
| Sharing knowledge | Unlimited access to our IT professionals community |
| Study advice | Our consultants are here for you to advice about your study career and options |
| Study materials | Certified teachers with in depth knowledge about the subject. |
| Service | World's best service |
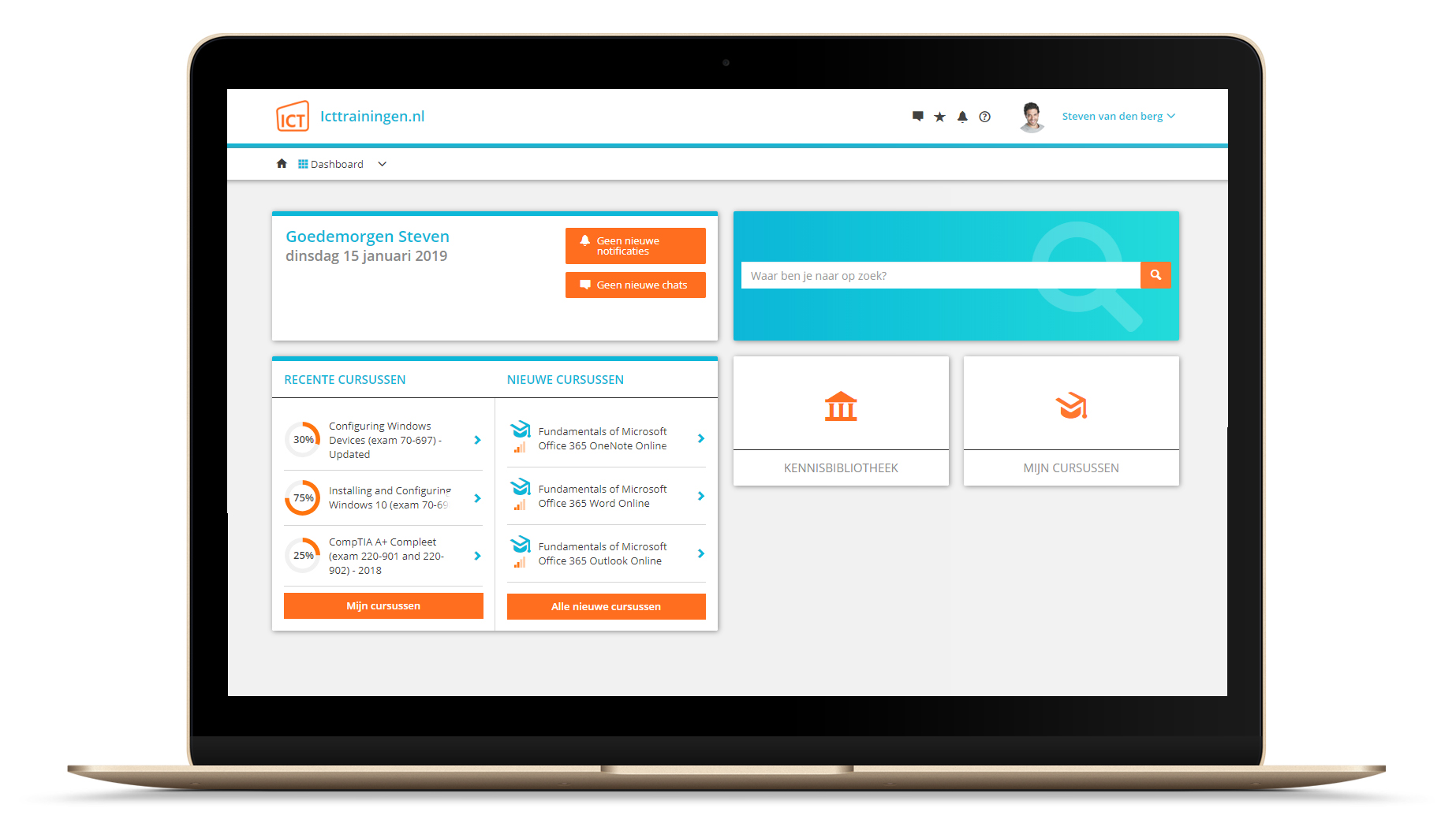
Platform
Na bestelling van je training krijg je toegang tot ons innovatieve leerplatform. Hier vind je al je gekochte (of gevolgde) trainingen, kan je eventueel cursisten aanmaken en krijg je toegang tot uitgebreide voortgangsinformatie.
FAQ
Niet gevonden wat je zocht? Bekijk alle vragen of neem contact op.