Course: IT Security for End Users
duration: 4 hours |
Language: English (US) |
access duration: 90 days |

Details
In this IT Security training course you will learn about security in the IT. You will learn how to deal with security threats with business computers and mobile devices and the options that are required to prevent thes attacks.
Finally you will learn how to reduce security risks and how to protect your computers and devices from hackers.
Result
After this course you will be familiar with IT Security for end users.
Prerequisites
There is no specific knowledge required.
Target audience
Helpdesk Operator, End users
Content
IT Security for End Users
IT Security for End Users: IT Security Fundamentals
- start the course
- describe what IT security is and what it includes
- identify the role and purpose of IT security in the corporate environment
- distinguish between confidentiality, integrity, and availability security objectives
- identify the end user's role in overall IT security
- describe general IT policy characteristics
- identify computer and hardware security policy best practices
- identify mobile device security policy best practices
- identify e-mail and Internet security policy best practices
- identify social networking security policy best practices
- identify password security policy best practices
- describe the specific security considerations for remote users
- identify remote user security policy best practices
- identify fundamental IT security best practices for the work environment
IT Security for End Users: Using Corporate Devices Securely
- start the course
- describe characteristics of human error threats to corporate computer security
- describe characteristics of malicious behavior that threatens corporate computer security
- identify best practices for protecting your corporate computer against malicious behavior
- describe characteristics and best practices for using file encryption and access controls to protect your corporate computer
- describe characteristics and best practices for using system patches to protect your corporate computer
- describe characteristics and best practices for using antivirus software to protect your corporate computer
- identify potential physical security threats to corporate mobile devices
- distinguish between the different types of malware threats
- identify characteristics of threats to mobile devices via wireless networks
- identify best practices for securing corporate mobile devices against common physical threats
- identify best practices for securing corporate mobile devices against common malware threats
- identify best practices for securing corporate mobile devices against common wireless network threats
- identify best practices for securing both corporate computers and corporate mobility devices against common threats
IT Security for End Users: Secure Corporate Communications and Networking
- start the course
- identify the threats to corporate security that can result from unsecured communications technologies
- identify the potential threats from unsecured e-mail usage
- describe best practices for ethical and safe e-mail use
- identify the common security threats to corporate systems and infrastructure from using unsecured webmail access at work
- identify best practices for securely accessing webmail services
- describe the common corporate security risks of Internet usage
- identify secure corporate Internet usage best practices
- identify characteristics and risks of social engineering scams
- describe techniques to avoid being a victim of social engineering scams
- identify risks to corporate systems from unsecured social networking activities
- identify best practices when using social networking platforms
- identify best practices for securely using corporate e-mail, access webmail, Internet use, and social networking activities
Course options
We offer several optional training products to enhance your learning experience. If you are planning to use our training course in preperation for an official exam then whe highly recommend using these optional training products to ensure an optimal learning experience. Sometimes there is only a practice exam or/and practice lab available.
Optional practice exam (trial exam)
To supplement this training course you may add a special practice exam. This practice exam comprises a number of trial exams which are very similar to the real exam, both in terms of form and content. This is the ultimate way to test whether you are ready for the exam.
Optional practice lab
To supplement this training course you may add a special practice lab. You perform the tasks on real hardware and/or software applicable to your Lab. The labs are fully hosted in our cloud. The only thing you need to use our practice labs is a web browser. In the LiveLab environment you will find exercises which you can start immediately. The lab enviromentconsist of complete networks containing for example, clients, servers,etc. This is the ultimate way to gain extensive hands-on experience.
Sign In
WHY_ICTTRAININGEN
Via ons opleidingsconcept bespaar je tot 80% op trainingen
Start met leren wanneer je wilt. Je bepaalt zelf het gewenste tempo
Spar met medecursisten en profileer je als autoriteit in je vakgebied.
Ontvang na succesvolle afronding van je cursus het officiële certificaat van deelname van Icttrainingen.nl
Krijg inzicht in uitgebreide voortgangsinformatie van jezelf of je medewerkers
Kennis opdoen met interactieve e-learning en uitgebreide praktijkopdrachten door gecertificeerde docenten
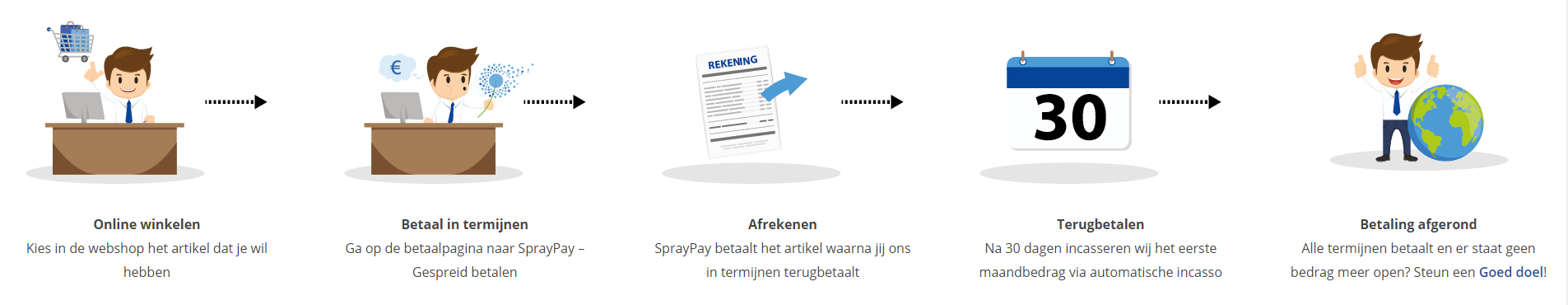
Orderproces
Once we have processed your order and payment, we will give you access to your courses. If you still have any questions about our ordering process, please refer to the button below.
read more about the order process
Een zakelijk account aanmaken
Wanneer u besteld namens uw bedrijf doet u er goed aan om aan zakelijk account bij ons aan te maken. Tijdens het registratieproces kunt u hiervoor kiezen. U heeft vervolgens de mogelijkheden om de bedrijfsgegevens in te voeren, een referentie en een afwijkend factuuradres toe te voegen.
Betaalmogelijkheden
U heeft bij ons diverse betaalmogelijkheden. Bij alle betaalopties ontvangt u sowieso een factuur na de bestelling. Gaat uw werkgever betalen, dan kiest u voor betaling per factuur.

Cursisten aanmaken
Als u een zakelijk account heeft aangemaakt dan heeft u de optie om cursisten/medewerkers aan te maken onder uw account. Als u dus meerdere trainingen koopt, kunt u cursisten aanmaken en deze vervolgens uitdelen aan uw collega’s. De cursisten krijgen een e-mail met inloggegevens wanneer zij worden aangemaakt en wanneer zij een training hebben gekregen.
Voortgangsinformatie
Met een zakelijk account bent u automatisch beheerder van uw organisatie en kunt u naast cursisten ook managers aanmaken. Beheerders en managers kunnen tevens voortgang inzien van alle cursisten binnen uw organisatie.
What is included?
| Certificate of participation | Yes |
| Monitor Progress | Yes |
| Award Winning E-learning | Yes |
| Mobile ready | Yes |
| Sharing knowledge | Unlimited access to our IT professionals community |
| Study advice | Our consultants are here for you to advice about your study career and options |
| Study materials | Certified teachers with in depth knowledge about the subject. |
| Service | World's best service |
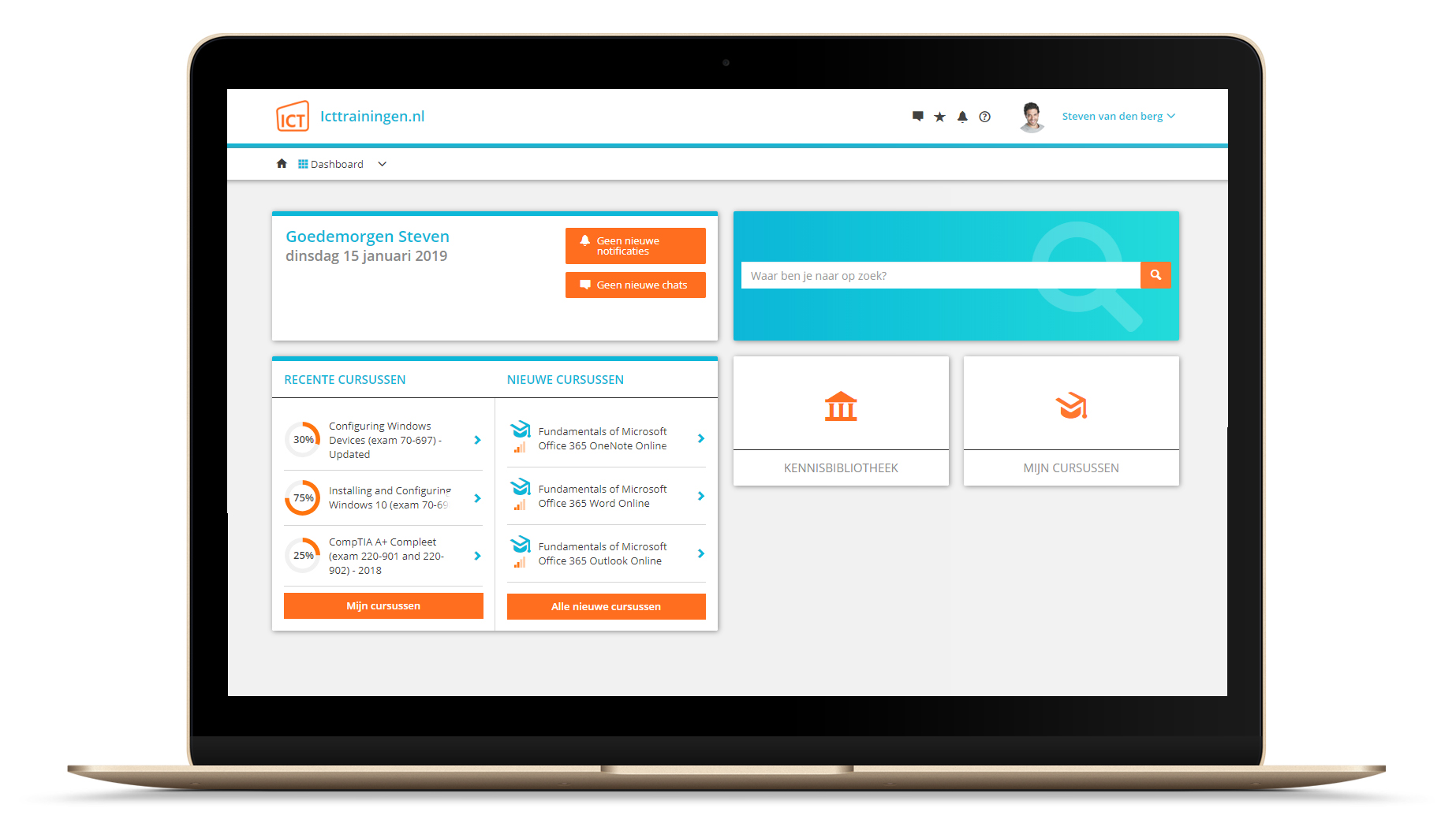
Platform
Na bestelling van je training krijg je toegang tot ons innovatieve leerplatform. Hier vind je al je gekochte (of gevolgde) trainingen, kan je eventueel cursisten aanmaken en krijg je toegang tot uitgebreide voortgangsinformatie.
FAQ
Niet gevonden wat je zocht? Bekijk alle vragen of neem contact op.