Complete package Microsoft Certified Azure Security Engineer Associate (AZ-500) - incl. exam (Update))
duration: 31 hours |
Language: English (US) |
access duration: 180 days |
Incompany available

Details
Are you interested in becoming a Microsoft Certified Azure Security Engineer Associate? In this training package you will be prepared for the AZ-500 exam.
Then this complete learning package is for you!
This course includes:
- Exam voucher (including resit)
- E-learning
- Practice exam
In the training you build the required knowledge and skills to implement security controls, you learn how you can continue to maintain your security status and how you identify system attacks, but you also repair them using the various security tools.
Finally, scripting and automation are treated as well as virtualization and cloud N-tier architecture.
The practice exam will then test your readiness to pass the AZ-500: Microsoft Azure Security Technologies exam. Our practice exams are designed to be as close as possible to the real certification exams. Both in content and in the form in which the questions are asked.
The course includes 1 exam voucher, which you can apply for via our support department. You need to request this during the training.
Result
After successful completion of this learning package:
- You can describe specialized data classifications on Azure.
- You can Identify Azure data protection mechanisms
- You can Implement azure data encryption methods.
- You know how to implement secure internet protocols on Azure.
- You can describe your Azure security services and functions.
- You can identify Azure data protection mechanisms.
Finally, you are optimally prepared for the AZ-500 exam. After passing the AZ-500 exam you will obtain the Microsoft Certified: Azure Security Engineer Associate certification.
Prerequisites
You have at least one year of practical experience with securing Azure work and experience with security controls for work with Azure.
Target audience
System Administrator, Network Administrator, Security Specialist
Content
Complete package Microsoft Certified Azure Security Engineer Associate (AZ-500) - incl. exam (Update))
Microsoft Azure Security Technologies: Exercising Governance Principles
The Azure hierarchy is made up of the Azure AD tenant, management groups, subscriptions, and resource groups containing the resources. Management groups provide a means to apply governance conditions for access, policies, and compliance to associated subscriptions. In this course, you will manage core elements of Azure Active Directory (AD). First, you will explore the relationship between Azure AD tenants and Azure subscriptions. Next, you will create a new AD tenant and switch between tenants. Then you will work with management groups and resource groups and learn to navigate through the Azure hierarchy. Finally, you will create an Azure AD custom domain name. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Managing Azure AD Users
Azure AD users can be managed in a variety of ways and should have an appropriate authentication method configured, such as multi-factor authentication (MFA). In this course, you will create and manage Azure AD user accounts including external guest accounts using the portal, the command line interface (CLI), and PowerShell. Then, you will use the Bulk Import service to create multiple Azure AD users at once. Finally, you will enable multi-factor authentication (MFA) for users and perform an MFA sign-in. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Securing Azure AD Users
Recognizing how authentication and authorization relate to identity federation, and understanding how to configure user authentication settings are key skills needed to secure your Azure AD users. In this course, you will review the relationship between authentication, authorization, and identity federation using external identity providers. Next, you will configure Azure AD identity protection and enable password authentication and protection. Then, you will configure single sign-on (SSO) and explore the Microsoft Entra admin center. Lastly, you will configure self-service password reset. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Managing Azure AD Groups
Azure AD groups can be managed using manual and dynamic member assignments and self-service group management. In this course, you will learn to manage Azure Active Directory (AD) groups through static group membership assignments using the portal, the CLI, and PowerShell. Then, you will work with Azure AD user attributes to determine dynamic group memberships. Lastly, you will enable and test self-service group management. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Managing Azure AD
Features such as access review, conditional access, and managed identities are used to manage Azure AD and secure the Azure environment. In this course, you will work with Azure Active (AD) access review and conditional access. Then, you will enable Azure AD password lockout and manage Azure AD roles. Next, you will work with Azure AD App registrations and privileged identity management. Lastly, you will work with service principals and managed identities. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Working with Azure AD Features
Microsoft Azure technicians can manage Azure AD devices and administrative units, product license and link an on-premises Microsoft Active Directory environment to an Azure AD tenant. In this course, you will manage Azure Active Directory (AD) product license assignments followed by joining a Windows station and a mobile device to Azure AD. Next, you will link an on-premises Microsoft Active Directory domain to Azure AD using Azure AD Connect. Lastly, you will manage Azure AD Connect and work with administrative units. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Restricting Resource Access with Roles
Access to Microsoft Azure resources is controlled through role assignments at specific levels in the Azure hierarchy. In this course, you will review how role-based access control (RBAC) is used within the Azure hierarchy. Next, you will learn to manage RBAC roles using the portal, the CLI, and PowerShell. Lastly, you will discover how to create a custom RBAC role, assign it to a user, and test role permissions when signed in to the Azure portal. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Configuring Azure Networking
Microsoft Azure technicians must plan, manage, and secure VNets just as they would manage physical on-premises networks. In this course, you will learn to create and manage VNets using the portal, the CLI, and PowerShell. Next, you will configure network watcher and network flow logs to capture network traffic. Then, you will work with Network Security Groups (NSGs) using the portal, the CLI, and PowerShell. Lastly, you will peer VNets together using the portal, the CLI, and PowerShell. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Implementing Azure Network Security
Controlling access into and out of network resources is one level of security that technicians can apply to help secure a Microsoft Azure environment. In this course, you will configure an application security group (ASG) and review how Azure Firewall and Firewall Manager work together. Then, you will configure firewall application, network, and network address translation (NAT) rules. Next, you will configure an application gateway and web application firewall. Lastly, you will discover when to use distributed denial-of-service (DDoS) protection and you will configure user defined routes (UDRs). This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Securing Network Access with VPNs
Linking an on-premises network to the Microsoft Azure cloud can be achieved in a variety of ways including virtual private networks (VPNs) and ExpressRoute circuits. In this course, you will review various types of VPNs and generate VPN public key infrastructure (PKI) certificates using PowerShell. Next, you will configure a site-to-site VPN and learn when to use virtual wide are network (WAN) and ExpressRoute dedicated circuits. Lastly, you will work with service endpoints, private links, and point-to-site VPNs. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Managing Azure Virtual Machines
Secure Shell (SSH) allows for secure remote management of Linux hosts. Further security measures such as jump boxes (Azure Bastion) prevent virtual machines from being reachable directly from the Internet. In this course, you will review how SSH public key authentication works and then generate SSH keys. Next, you will configure Linux SSH public key authentication and manage virtual machines (VMs) through Azure Bastion. Then, you will enable just-in-time access, add extensions to virtual machines and control access to virtual machines using role-based access control (RBAC) role assignments. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Managing Azure Storage
Storage account blob features such as versioning, soft deletion, and legal holds can keep organizations aligned with business needs related to regulatory compliance. Controlling storage account access and managing VM disks in a secured manner can prevent unauthorized access. In this course, you will work with storage account features such as versioning and soft deletion. Then, you will configure a storage account legal hold and network access. Next, you will work with lifecycle management, access keys, and shared access signatures (SAS). Lastly, you will manage Azure Tables and Storage Explorer and attach a disk to a virtual machine. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Managing Azure Files Shares
Microsoft Azure Files shared folders provide a cloud-central method of sharing files with Linux and Windows hosts. In this course, you will learn to configure Azure Files Share shared folders using the portal, the CLI, and PowerShell. Then, you will map a drive letter from Windows to an Azure Files share. Finally, you will use Linux to mount an Azure Files share. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Securing Azure Databases
Securing Azure-based SQL database deployments uses many features available on-premises, including external user authentication and data sensitivity labels. In this course, you will deploy and manage Azure SQL-based solutions. Then, you will manage SQL login credentials and enable Azure Active Directory (AD) database authentication. Next, you will configure various Azure SQL settings and high availability. Lastly, you will work with SQL data sensitivity labels an allow SQL role access through the portal, the CLI, and PowerShell. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Implementing Data Security
Implementing data security in Microsoft Azure spans all services including storage account data classification and encryption, database data masking, and the use of public key infrastructure (PKI) to secure HTTPS connections. In this course, you will explore how encryption provides data confidentiality, along with the various regulations related to data privacy. Next, you will use Microsoft Purview Governance to classify data. Then, you will enable data masking, disk encryption, and storage account encryption. Finally, you will examine how PKI certificates secure computing environments, identify how Transport Layer Security (TLS) secures network communications, and configure an HTTPS binding. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Working with Azure Applications
Deploying and managing functions and web apps in Azure is possible by using logic apps, Azure web apps, blueprints for setting up cloud environments, and by placing app content near users via a content delivery network (CDN). In this course, you will deploy and manage Azure Web Applications (App Services) using the portal and Visual Studio. Next, you will compare security baselines to an Azure web app, and create an Azure function app and an Azure logic app. Then you will work with Azure Blueprints, Azure app external authentication, network restrictions, and custom DNS domain names. Finally, you will configure a content delivery network. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Managing Containerized Applications
Microsoft Azure technicians can secure containerized applications and Kubernetes clusters using a variety of methods, including Azure Active Directory (AD) authentication and role-based access control (RBAC). In this course, you will identify how to use application containerization within the Microsoft Azure environment. Then, you will configure Docker on Linux and Windows hosts and build a Docker container image from a Dockerfile. Next, you will configure an Azure Container Registry, deploy Azure Container Instances (ACIs), and manage an Azure Kubernetes Service (AKS) cluster. Lastly, you will enable Azure AD authentication for AKS and configure AKS RBAC roles. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Managing Key Vault Secrets
Many Microsoft Azure services require credentials to access a variety of Azure resources. Azure Key Vault provides a secure centralized storage solution for these types of secrets. In this course, you will work with Azure key vaults. First, you will create a key vault and manage key vault secrets using the portal, the command line interface (CLI), and PowerShell. Next, you will work with public key infrastructure (PKI) certificates using the portal, the CLI and PowerShell. Lastly, you will review how hardware security modules (HSMs) work in Azure. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Managing Azure Policies
One way to achieve overall governance and regulatory compliance with Microsoft Azure is through the use of Azure Policy. In this course, you will work with Azure Policy to control Azure functionality and to check for compliance. First, you will explore how Azure Policy can be used for compliance. Then you will create policy assignments to check for Azure resource compliance with specific settings. Next, you will create and assign a custom policy to the Azure hierarchy. Finally, you will assign policy groups (policy initiatives) to the Azure hierarchy. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft Azure Security Technologies: Enabling Resource Locking
Microsoft Azure technicians can prevent the unintended deletion of Azure resources using the resource lock feature. In this course you will learn to protect, or lock, Azure resources to prevent modifications and deletions. First, you will review how resource locking works. Then, you will manage resource locks throughout the Azure hierarchy using the portal, the CLI, and PowerShell. Next, you will enable resource locking using an Azure Resource Manager (ARM) template and test the resulting implications. This course can be used to prepare for exam AZ-500, Microsoft Azure Security Technologies.
Microsoft - AZ-500 : Microsoft Azure Security Technologies
Microsoft - AZ-500 : Microsoft Azure Security Technologies
Course options
We offer several optional training products to enhance your learning experience. If you are planning to use our training course in preperation for an official exam then whe highly recommend using these optional training products to ensure an optimal learning experience. Sometimes there is only a practice exam or/and practice lab available.
Optional practice exam (trial exam)
To supplement this training course you may add a special practice exam. This practice exam comprises a number of trial exams which are very similar to the real exam, both in terms of form and content. This is the ultimate way to test whether you are ready for the exam.
Optional practice lab
To supplement this training course you may add a special practice lab. You perform the tasks on real hardware and/or software applicable to your Lab. The labs are fully hosted in our cloud. The only thing you need to use our practice labs is a web browser. In the LiveLab environment you will find exercises which you can start immediately. The lab enviromentconsist of complete networks containing for example, clients, servers,etc. This is the ultimate way to gain extensive hands-on experience.
Sign In
WHY_ICTTRAININGEN
Via ons opleidingsconcept bespaar je tot 80% op trainingen
Start met leren wanneer je wilt. Je bepaalt zelf het gewenste tempo
Spar met medecursisten en profileer je als autoriteit in je vakgebied.
Ontvang na succesvolle afronding van je cursus het officiële certificaat van deelname van Icttrainingen.nl
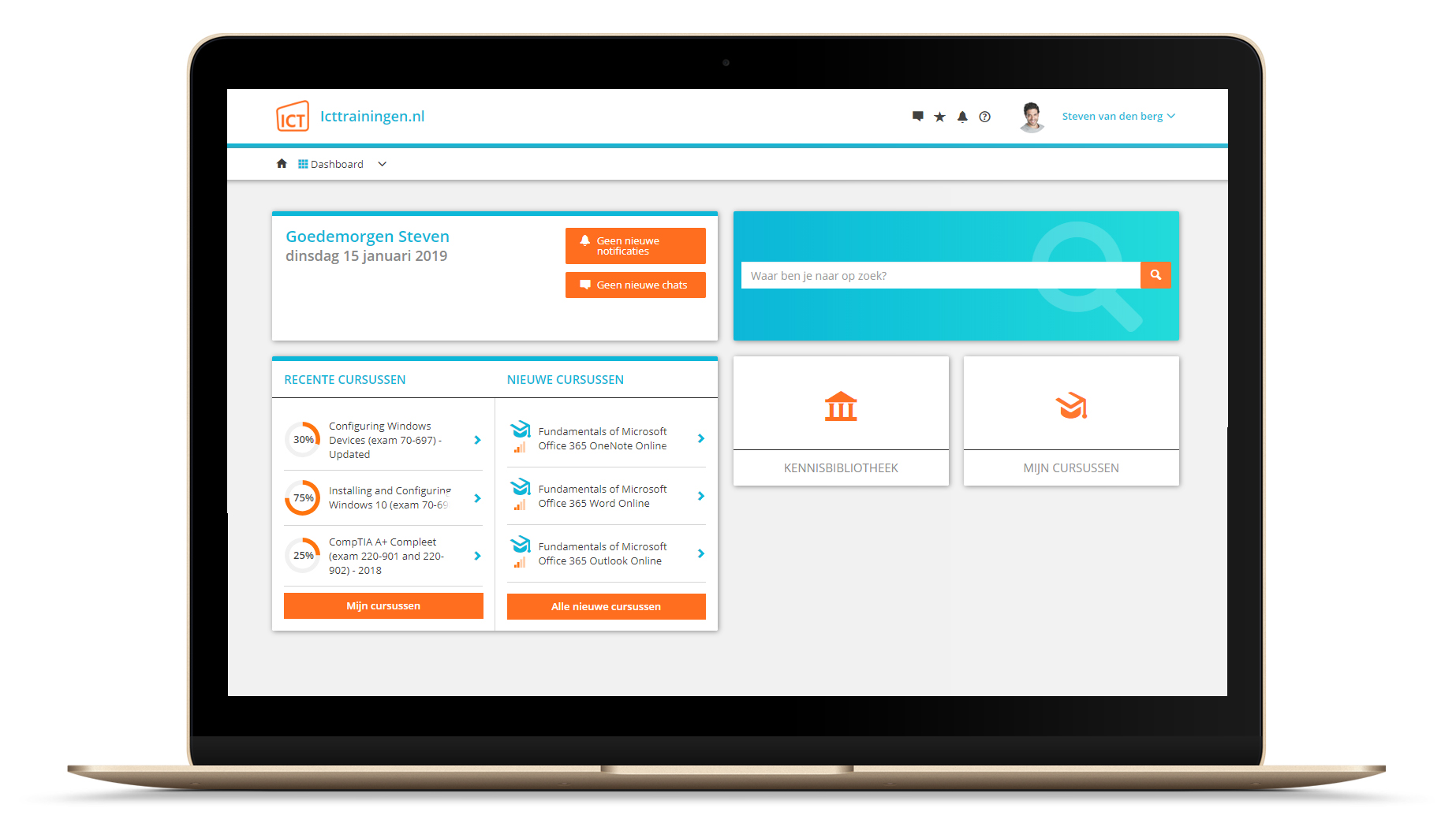
Krijg inzicht in uitgebreide voortgangsinformatie van jezelf of je medewerkers
Kennis opdoen met interactieve e-learning en uitgebreide praktijkopdrachten door gecertificeerde docenten
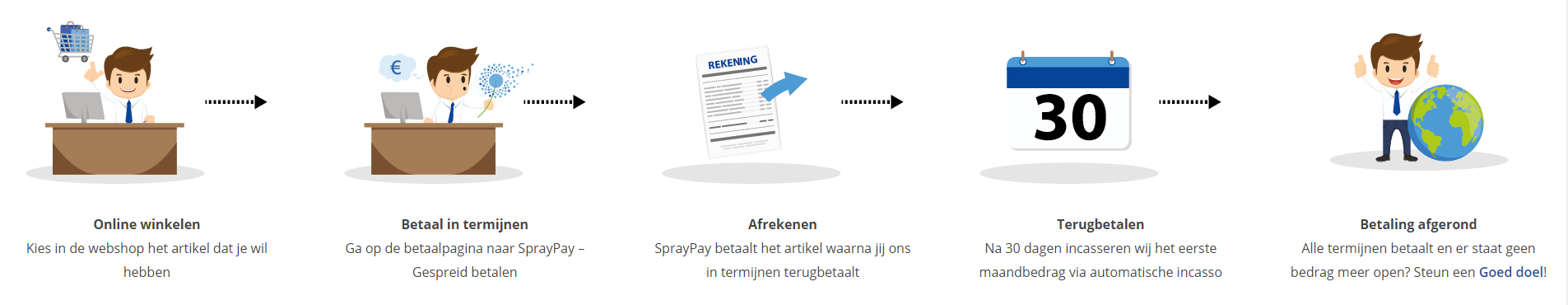
Orderproces
Once we have processed your order and payment, we will give you access to your courses. If you still have any questions about our ordering process, please refer to the button below.
read more about the order process
Een zakelijk account aanmaken
Wanneer u besteld namens uw bedrijf doet u er goed aan om aan zakelijk account bij ons aan te maken. Tijdens het registratieproces kunt u hiervoor kiezen. U heeft vervolgens de mogelijkheden om de bedrijfsgegevens in te voeren, een referentie en een afwijkend factuuradres toe te voegen.
Betaalmogelijkheden
U heeft bij ons diverse betaalmogelijkheden. Bij alle betaalopties ontvangt u sowieso een factuur na de bestelling. Gaat uw werkgever betalen, dan kiest u voor betaling per factuur.

Cursisten aanmaken
Als u een zakelijk account heeft aangemaakt dan heeft u de optie om cursisten/medewerkers aan te maken onder uw account. Als u dus meerdere trainingen koopt, kunt u cursisten aanmaken en deze vervolgens uitdelen aan uw collega’s. De cursisten krijgen een e-mail met inloggegevens wanneer zij worden aangemaakt en wanneer zij een training hebben gekregen.
Voortgangsinformatie
Met een zakelijk account bent u automatisch beheerder van uw organisatie en kunt u naast cursisten ook managers aanmaken. Beheerders en managers kunnen tevens voortgang inzien van alle cursisten binnen uw organisatie.
What is included?
| Certificate of participation | Yes |
| Monitor Progress | Yes |
| Mobile ready | Yes |
| Sharing knowledge | Unlimited access to our IT professionals community |
| Study advice | Our consultants are here for you to advice about your study career and options |
| Study materials | Certified teachers with in depth knowledge about the subject. |
| Service | World's best service |
Platform
Na bestelling van je training krijg je toegang tot ons innovatieve leerplatform. Hier vind je al je gekochte (of gevolgde) trainingen, kan je eventueel cursisten aanmaken en krijg je toegang tot uitgebreide voortgangsinformatie.
FAQ
Niet gevonden wat je zocht? Bekijk alle vragen of neem contact op.