Course: Prompt Engineering voor Ethical Hacking
duration: 21 hours |
Language: English (US) |
access duration: 180 days |

Details
The cybersecurity landscape is constantly changing, with new threats and impact from new, powerful technologies. This course takes the established Ethical Hacking certification framework and introduces artificial intelligence.
You'll delve into the core concepts of ethical hacking while learning about the capabilities offered by advanced areas such as Prompt Engineering and Generative AI.
Result
After following this course you will be able to:
- Apply the basic principles of ethical hacking.
- Recognize the latest developments in artificial intelligence (AI) in the field of cybersecurity.
- Use prompt engineering and generative AI in an ethical hacking context.
Prerequisites
Some experience in ehtical hacking is recommended.
Target audience
Security Specialist
Content
Prompt Engineering voor Ethical Hacking
Prompt Engineering: Ethical Hacking & Generative AI Fusion
In our increasingly digital world, the convergence of ethical hacking and generative AI technologies has become a crucial frontier in cybersecurity. As technology advances, so do the methods employed by hackers, making it essential for ethical hackers, or white hat hackers, to stay one step ahead. This course introduces you to the exciting world of ethical hacking and generative AI technologies. You will gain insights into the evolving cybersecurity landscape, learn about the techniques used by both malicious and ethical hackers, and explore how generative AI can be leveraged for both offensive and defensive purposes. By the end of this course, you will be equipped with a solid foundation in ethical hacking and generative AI, enabling you to understand the complex dynamics between security and innovation in the digital age.
Prompt Engineering: Generative AI for Reconnaissance
In today's rapidly evolving digital landscape, the convergence of ethical hacking and generative AI has emerged as a powerful force in countering cybersecurity threats. As malicious hackers adapt and exploit advanced technologies, the need for innovative defenses becomes paramount. This course explores the cutting-edge domain of generative artificial intelligence (AI) and reconnaissance techniques. In this course, you will explore reconnaissance techniques leveraging AI's potential and apply passive and active reconnaissance techniques. Next, you'll explore the challenges and solutions associated with reconnaissance and generative AI and consider the methods used to protect against it. Finally, you'll explore how ethical hackers can use the information obtained during reconnaissance.
Prompt Engineering: Generative AI for Scanning & Enumeration
In today's dynamic and evolving digital terrain, the need for robust cybersecurity measures has never been more critical. As technology continues to advance, hackers are constantly adapting their methods, making it imperative for ethical hackers to stay one step ahead. This course explores the convergence of ethical hacking and generative AI, specifically focusing on the scanning and enumeration phase of the ethical hacking process. You will begin by examining the network scanning phase of the ethical hacking process and how generative AI and prompt engineering enhance this process. With a solid foundation, you will then discover ways that prompt engineering can optimize scanning, the risks and benefits of using AI-assisted scanning, and how generative AI can boost various scanning techniques. Finally, you will take a look at realistic examples involving scanning and enumeration techniques, focusing on the role that generative AI plays in these scenarios.
Prompt Engineering: Generative AI for System Hacking
In a world increasingly reliant on interconnected systems, safeguarding them from malicious actors is critical. Ethical hackers are key to maintaining a robust cybersecurity posture, and must commit to continuous improvement to stay ahead of malicious actors. This course provides an immersive journey into the techniques and methodologies employed by ethical hackers to protect and secure systems while focusing on generative artificial intelligence (AI) as a transformative resource in the hacking toolchain. You will start by exploring the fundamental concepts and methodologies that underpin system hacking and how generative AI can enhance hacking techniques and countermeasures. With this foundation in place, you'll investigate how to enhance attacks with generative AI, protect against system hacking by detecting vulnerabilities, use AI to drive penetration tests, and recognize the impact generative AI has on system hacking. Finally, you'll explore real-world system hacking scenarios and reflect on the transformative potential of generative AI.
Prompt Engineering: Generative AI for Malware & Social Engineering
In the dynamic digital landscape, cybersecurity is more important than ever. Malicious actors are well aware that people are often the weakest link in an organization's cybersecurity posture. Ethical hackers commit significant effort into penetration testing and strategizing to combat malware and social engineering efforts executed by threat actors. This course journeys deep into the techniques and methodologies employed by ethical hackers to uncover malware and educate users in the ongoing battle against social engineering and how generative artificial intelligence (AI) can assist them in this pursuit. You'll start by exploring the types of malware and social engineering principles and techniques. With this foundation, you'll explore how generative AI can be used to help detect malware and social engineering attacks. You'll discover potential damage that can result from such attacks along with countermeasures that can be taken and then you'll explore proactive efforts to train users about social engineering attacks. You'll investigate how to use generative AI and prompt engineering to counter malware and social engineering, and you'll proceed to explore how malware and social engineering evolve over time. Lastly, you'll examine some real-world case studies that feature malware and social engineering attacks.
Prompt Engineering: GenAI's Impact on Network & Perimeter Ethical Hacking
In the digital era, boundaries are constantly being redefined. Our networks, once clear and tangible, have been blurred by the advent of cloud technology, Internet of Things (IoT), and a myriad of interconnected systems. As these boundaries shift, the methods employed to breach them also evolve. To fortify our defenses and safeguard ever-expanding perimeters, it becomes critical for organizations to harness cutting-edge advancements, such as generative artificial intelligence (AI), to envision, predict, and counteract these emerging threats. Begin by exploring the fundamentals of network and perimeter hacking, typical network attack techniques, and how these attacks can be enhanced using generative AI. You will investigate AI-assisted countermeasures, examine how AI impacts both attack and defensive posture, and assess the effectiveness of network security hardware and software. You will use generative AI for enhanced network vulnerability discovery of wired and wireless networks and conduct a simulated AI-driven attack on a wired network. Finally, you will discover why network and perimeter security is so important and assess real-world case studies involving network and perimeter hacking.
Prompt Engineering: Web Application & Database Hacking in the Age of GenAI
This course is a comprehensive journey into the tools and techniques available to ethical hackers to discover vulnerabilities and weaknesses in web applications and databases. Particular attention will be paid to how generative artificial intelligence (AI) can help in the discovery and mitigation of attacks on these technologies, including those enhanced by integrating AI in the attack. You'll start by exploring common web application and database vulnerabilities and how they are exploited and mitigated. You'll also examine common database hacking techniques. Next, you will explore how generative AI can be applied to enhance the security of web applications and databases and you will conduct a generative AI-assisted SQL injection attack in a simulated environment. Then, you'll explore strategies to secure Web applications and databases and use generative AI and prompt engineering to detect and address vulnerabilities in a web application. You'll explore the implications of AI-enhanced Web and database hacking and consider the importance of regular updates and patches. Lastly, you'll review and assess real-world case studies of web application and database hacking and focus on the potential impact of generative AI on such attacks.
Prompt Engineering: Cloud Computing & IoT Hacking in the Era of GenAI
As the digital revolution marches forward, cloud computing and the Internet of Things (IoT) have taken center stage in transforming our world into a seamlessly interconnected ecosystem. This course dives deep into the interplay between Cloud computing, IoT, and generative artificial intelligence (AI), shedding light on their collective vulnerabilities and potential and demonstrating how generative AI can be both a formidable adversary and a powerful ally. You will begin by exploring common cloud service and IoT device vulnerabilities and how generative AI can help in either exploiting their respective vulnerabilities or protecting against such weaknesses. Then, you will then conduct a simulated hack against a cloud-based service with the assistance of generative AI. Next, you'll identify security best practices for cloud and IoT devices and evaluate security measures for cloud services and IoT devices. You'll employ generative AI to identify and mitigate IoT device vulnerabilities and you'll discover trends and advancements in cloud and IoT security and the role of generative AI. Finally, you will explore real-world case studies involving cloud and IoT hacking focusing on the potential impact of generative AI on these attacks.
Prompt Engineering: Mobile Platform Security in the GenAI Era
Mobile devices are involved in vast facets of our daily lives, and as these devices and AI evolve, they become powerful tools and vulnerable gateways. With AI-driven functionalities at the forefront of mobile technology innovation, understanding the security implications and nuances is paramount. In this course, explore common mobile platform vulnerabilities and utilize generative AI to bolster mobile security measures. Next, learn how to execute mobile attacks with generative AI, evaluate mobile security measures, and use generative AI to identify and patch app vulnerabilities. Finally, examine the impact of AI-enhanced mobile hacking, the importance of regular updates and patches, and real-world mobile hacking case studies. Upon completion, you'll be able to outline the intricate landscape of mobile security and the implications of integrating generative AI.
Prompt Engineering: Covering Tracks with GenAI
As cyber threats become more sophisticated, the art of evading detection, covering one's tracks, and maintaining access becomes an essential craft for every ethical hacker. The potential of artificial intelligence (AI) to revolutionize clandestine operations in cybersecurity cannot be overlooked. This course examines the fusion of traditional stealth techniques in hacking with the cutting-edge capabilities of generative AI, looking at how generative AI can be harnessed to leave no digital footprint, ensuring prolonged access to compromised systems. You'll begin by exploring the techniques used by hackers to maintain access and the role of generative AI in detecting and mitigating attempts to cover tracks. You'll orchestrate a generative AI-assisted operation to cover tracks in a simulated environment and use generative AI to identify signs of advanced track-covering activities. Next, you'll identify the implications of failing to cover tracks, and of maintaining prolonged access to compromised systems. Lastly, you'll analyze and evaluate real-world case studies focusing on the potential impact of generative AI.
Final Exam: Prompt Engineering for Ethical Hacking
Final Exam: Prompt Engineering for Ethical Hacking will test your knowledge and application of the topics presented throughout the Prompt Engineering for Ethical Hacking journey.
Course options
We offer several optional training products to enhance your learning experience. If you are planning to use our training course in preperation for an official exam then whe highly recommend using these optional training products to ensure an optimal learning experience. Sometimes there is only a practice exam or/and practice lab available.
Optional practice exam (trial exam)
To supplement this training course you may add a special practice exam. This practice exam comprises a number of trial exams which are very similar to the real exam, both in terms of form and content. This is the ultimate way to test whether you are ready for the exam.
Optional practice lab
To supplement this training course you may add a special practice lab. You perform the tasks on real hardware and/or software applicable to your Lab. The labs are fully hosted in our cloud. The only thing you need to use our practice labs is a web browser. In the LiveLab environment you will find exercises which you can start immediately. The lab enviromentconsist of complete networks containing for example, clients, servers,etc. This is the ultimate way to gain extensive hands-on experience.
Sign In
WHY_ICTTRAININGEN
Via ons opleidingsconcept bespaar je tot 80% op trainingen
Start met leren wanneer je wilt. Je bepaalt zelf het gewenste tempo
Spar met medecursisten en profileer je als autoriteit in je vakgebied.
Ontvang na succesvolle afronding van je cursus het officiële certificaat van deelname van Icttrainingen.nl
Krijg inzicht in uitgebreide voortgangsinformatie van jezelf of je medewerkers
Kennis opdoen met interactieve e-learning en uitgebreide praktijkopdrachten door gecertificeerde docenten
Orderproces
Once we have processed your order and payment, we will give you access to your courses. If you still have any questions about our ordering process, please refer to the button below.
read more about the order process
Een zakelijk account aanmaken
Wanneer u besteld namens uw bedrijf doet u er goed aan om aan zakelijk account bij ons aan te maken. Tijdens het registratieproces kunt u hiervoor kiezen. U heeft vervolgens de mogelijkheden om de bedrijfsgegevens in te voeren, een referentie en een afwijkend factuuradres toe te voegen.
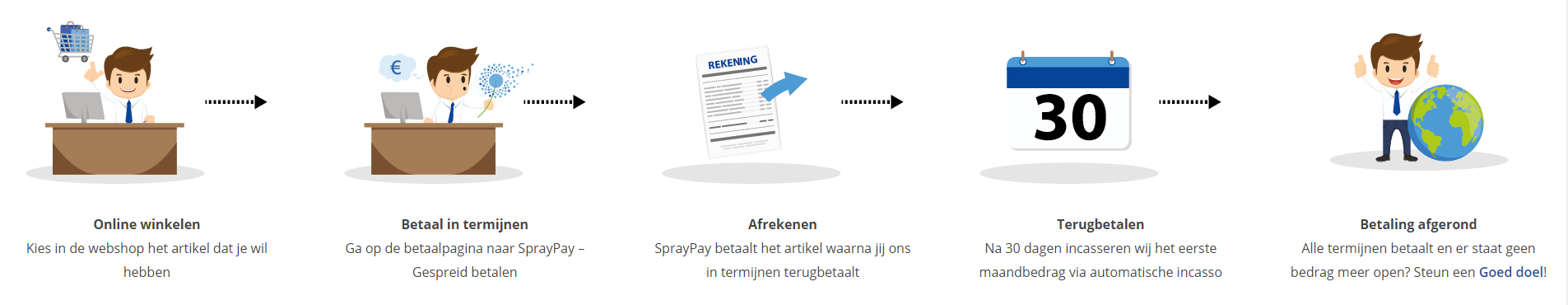
Betaalmogelijkheden
U heeft bij ons diverse betaalmogelijkheden. Bij alle betaalopties ontvangt u sowieso een factuur na de bestelling. Gaat uw werkgever betalen, dan kiest u voor betaling per factuur.

Cursisten aanmaken
Als u een zakelijk account heeft aangemaakt dan heeft u de optie om cursisten/medewerkers aan te maken onder uw account. Als u dus meerdere trainingen koopt, kunt u cursisten aanmaken en deze vervolgens uitdelen aan uw collega’s. De cursisten krijgen een e-mail met inloggegevens wanneer zij worden aangemaakt en wanneer zij een training hebben gekregen.
Voortgangsinformatie
Met een zakelijk account bent u automatisch beheerder van uw organisatie en kunt u naast cursisten ook managers aanmaken. Beheerders en managers kunnen tevens voortgang inzien van alle cursisten binnen uw organisatie.
What is included?
| Certificate of participation | Yes |
| Monitor Progress | Yes |
| Award Winning E-learning | Yes |
| Mobile ready | Yes |
| Sharing knowledge | Unlimited access to our IT professionals community |
| Study advice | Our consultants are here for you to advice about your study career and options |
| Study materials | Certified teachers with in depth knowledge about the subject. |
| Service | World's best service |
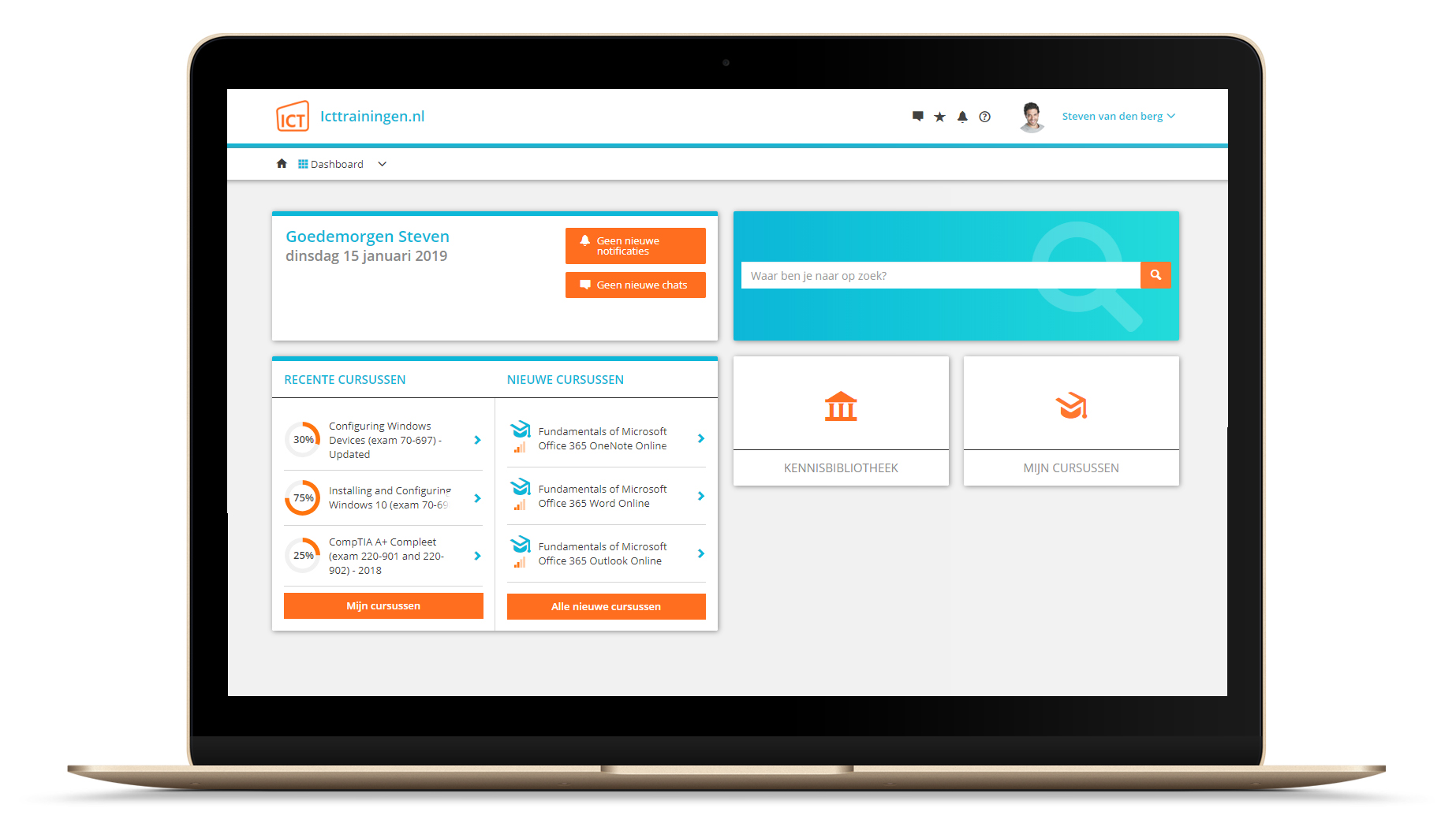
Platform
Na bestelling van je training krijg je toegang tot ons innovatieve leerplatform. Hier vind je al je gekochte (of gevolgde) trainingen, kan je eventueel cursisten aanmaken en krijg je toegang tot uitgebreide voortgangsinformatie.
FAQ
Niet gevonden wat je zocht? Bekijk alle vragen of neem contact op.